What is telescoping?
Note 1: ETH::A&D
Deck: ETH::A&D
Note Type: Horvath Classic
GUID:
modified
Note Type: Horvath Classic
GUID:
c9U$4,GAT:
Before
Front
Back
What is telescoping?
By plugging in previous terms into a recursive definition we can get a feel for it's asymptotic runtime. This is only for intuiton, not a proof
\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth.
\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth.
After
Front
What is telescoping?
Back
What is telescoping?
By plugging in previous terms into a recursive definition we can get a feel for it's asymptotic runtime. This is only for intuiton, not a proof.
\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth.
\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | By plugging in previous terms into a recursive definition we can get a feel for it's asymptotic runtime. <i>This is only for intuiton, not a proof</i> <br><br>\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth. | By plugging in previous terms into a recursive definition we can get a feel for it's asymptotic runtime. <i>This is only for intuiton, not a proof.</i> <br><br>\(M(n + 1) = 3 \cdot M(n)\) turns into \(M(n + 1) = 3 \cdot (3 \cdot M(n - 1))\) and so on and so forth. |
Note 2: ETH::A&D
Deck: ETH::A&D
Note Type: Horvath Classic
GUID:
modified
Note Type: Horvath Classic
GUID:
qBT+Ifr6uX
Before
Front
In what situation is the array the correct datastructure?
Back
In what situation is the array the correct datastructure?
When we have a fixed upper bound for the size of the list.
After
Front
In what situation is the array the correct underlying datastructure for a list?
Back
In what situation is the array the correct underlying datastructure for a list?
When we have a fixed upper bound for the size of the list.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | In what situation is the array the correct datastructure? | In what situation is the array the correct underlying datastructure for a list? |
Note 3: ETH::DiskMat
Deck: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
modified
Note Type: Horvath Cloze
GUID:
i
Before
Front
A monoid has the following properties:
Back
A monoid has the following properties:
- closure
- associativity
- identity
After
Front
A monoid has the following properties:
- Closure
- Associativity
- Identity
Back
A monoid has the following properties:
- Closure
- Associativity
- Identity
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | A <b>monoid</b> has the following properties: | A <b>monoid</b> has the following properties:<br><ol><li>{{c1::Closure}}</li><li>{{c2::Associativity}}</li><li>{{c3::Identity}}</li></ol> |
| Extra |
Note 4: ETH::DiskMat
Deck: ETH::DiskMat
Note Type: Horvath Classic
GUID:
modified
Note Type: Horvath Classic
GUID:
uCGhOduc{_
Before
Front
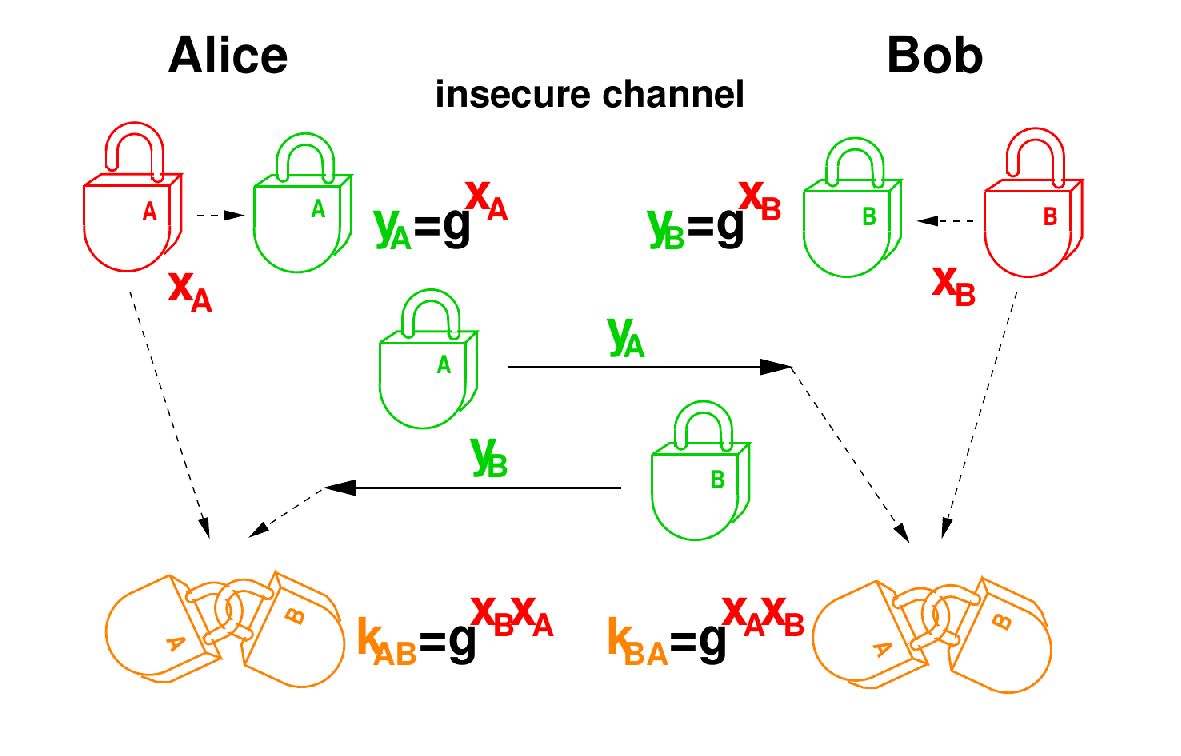
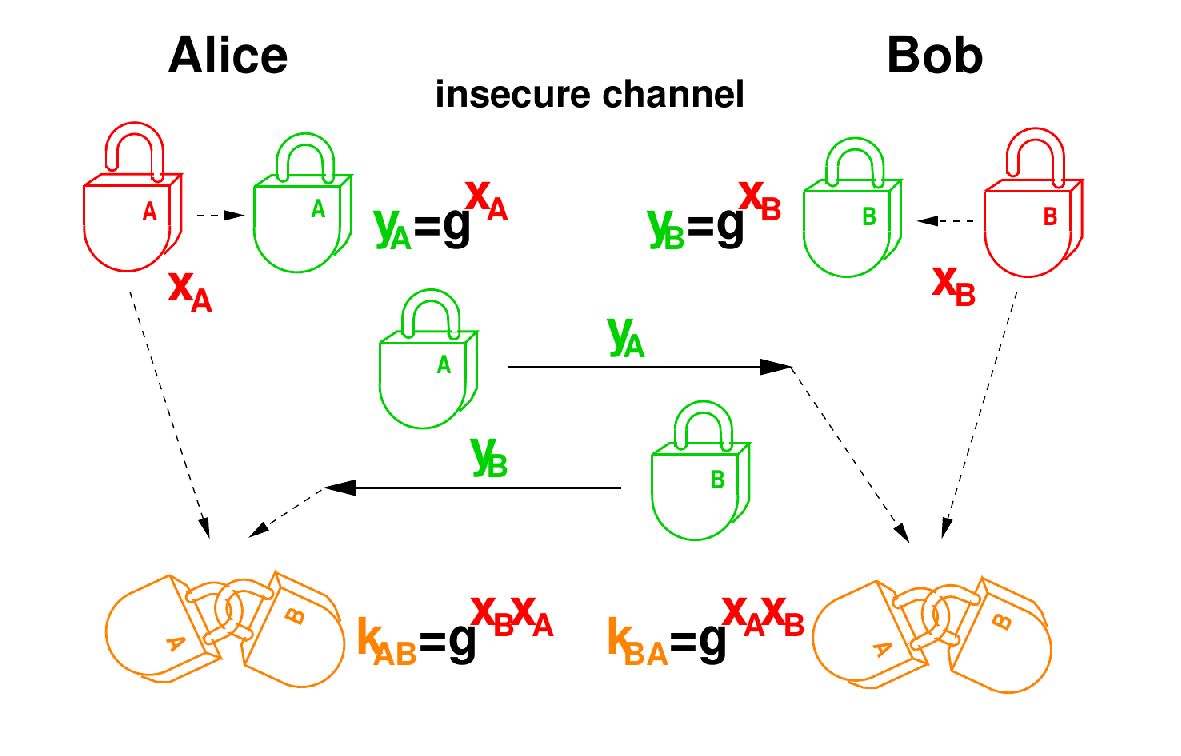
Explain the mechanical analog of the Diffie-Hellman protocol.
Back
Explain the mechanical analog of the Diffie-Hellman protocol.
After
Front
Explain the mechanical analog of the Diffie-Hellman protocol.
Back
Explain the mechanical analog of the Diffie-Hellman protocol.
A padlock without a key.
Alice and Bob can exchange their locks (closed) and keep a copy in the open state. Then they can both generate the same configuration, namely the two locks interlocked. For the adversary, this is impossible without breaking open one of the locks.
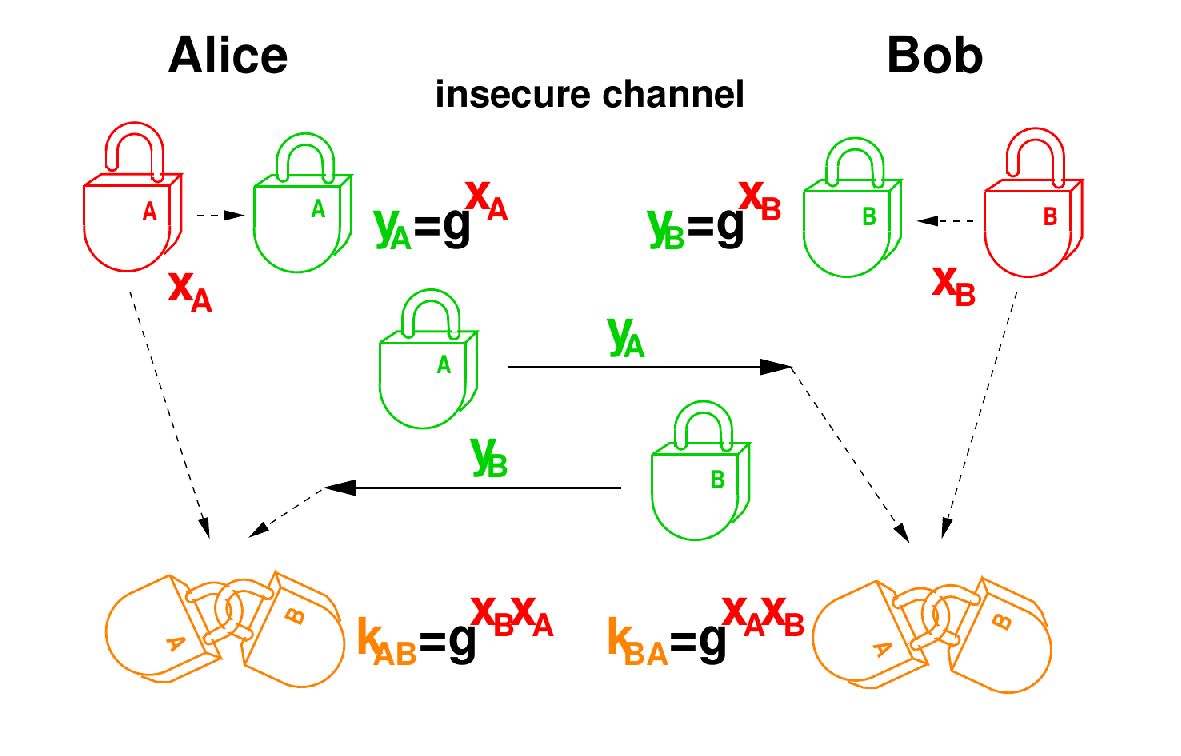
Alice and Bob can exchange their locks (closed) and keep a copy in the open state. Then they can both generate the same configuration, namely the two locks interlocked. For the adversary, this is impossible without breaking open one of the locks.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | <img src="paste-39931b24c512906843c903f461b7c1cc9f5a6685.jpg"> | A padlock without a key.<br><br>Alice and Bob can exchange their locks (closed) and keep a copy in the open state. Then they can both generate the same configuration, namely the two locks interlocked. For the adversary, this is impossible without breaking open one of the locks.<br><br><img src="paste-39931b24c512906843c903f461b7c1cc9f5a6685.jpg"> |
Note 5: ETH::DiskMat
Deck: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
modified
Note Type: Horvath Cloze
GUID:
uK|j,XZw5[
Before
Front
For DHKE, both Alice and Bob choose \(x_A, x_B\) (their private keys) at random.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and with \(y_B\)analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and with \(y_B\)analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Back
For DHKE, both Alice and Bob choose \(x_A, x_B\) (their private keys) at random.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and with \(y_B\)analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and with \(y_B\)analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
After
Front
For DHKE, both Alice and Bob choose \(x_A, x_B\) (their private keys) at random.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Back
For DHKE, both Alice and Bob choose \(x_A, x_B\) (their private keys) at random.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | For DHKE, both Alice and Bob {{c1:: choose \(x_A, x_B\) (their private keys) at random}}.<br>They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and |
For DHKE, both Alice and Bob {{c1:: choose \(x_A, x_B\) (their private keys) at random}}.<br><br>They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is {{c2:: sent over the network to their partner}}.<br><br>The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}. |
Note 6: ETH::DiskMat
Deck: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
modified
Note Type: Horvath Cloze
GUID:
xelDz|Gp*?
Before
Front
A right (left) neutral element is an elements such that for all \(a \in G\), \(a*e = a\) (\(e*a = a\)).
Back
A right (left) neutral element is an elements such that for all \(a \in G\), \(a*e = a\) (\(e*a = a\)).
After
Front
A right (left) neutral element is an element such that for all \(a \in G\), \(a*e = a\) (\(e*a = a\)).
Back
A right (left) neutral element is an element such that for all \(a \in G\), \(a*e = a\) (\(e*a = a\)).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <div>A {{c1::right (left) neutral element}} |
<div>A {{c1::right (left) neutral element}} is an element such that for all \(a \in G\), {{c2:: \(a*e = a\) (\(e*a = a\))}}.</div> |