- search(x, W) returns the position of the key x in memory
- insert(x, W) Insert the key x into W, as long as it’s not saved there yet
- delete(x, W) find and delete the key x from W
Note 1: ETH::A&D
Note Type: Horvath Cloze
GUID:
J5>uyKCn19
Previous
Note did not exist
New Note
Front
Back
- search(x, W) returns the position of the key x in memory
- insert(x, W) Insert the key x into W, as long as it’s not saved there yet
- delete(x, W) find and delete the key x from W
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | The ADT Dictionary implements the following methods:<br><ul><li>{{c1::<b>search(x, W)</b> returns the position of the key x in memory}}</li><li>{{c2::<b>insert(x, W)</b> Insert the key <b>x</b> into <b>W</b>, as long as it’s not saved there yet}}<br></li><li>{{c3::<b>delete(x, W)</b> find and delete the key <b>x</b> from <b>W</b>}}<br></li></ul> |
Note 2: ETH::A&D
Note Type: Horvath Cloze
GUID:
M11/nZaHIu
Previous
Note did not exist
New Note
Front
| search | insert | delete | |
| unsorted Array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| sorted Array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| DLL | \(O(n)\) (no bin. search possible) | \(O(1)\) | \(O(n)\) |
Back
| search | insert | delete | |
| unsorted Array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| sorted Array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| DLL | \(O(n)\) (no bin. search possible) | \(O(1)\) | \(O(n)\) |
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <b></b><b></b><b></b><b></b><table> <tbody><tr> <td></td> <td><b>search</b></td> <td><b>insert</b></td> <td><b>delete</b></td> </tr> <tr> <td>unsorted Array</td> <td>{{c1::\(O(n)\)}}</td> <td>{{c2::\(O(1)\)}}</td> <td>{{c3::\(O(n)\)}}</td> </tr> <tr> <td>sorted Array</td> <td>{{c4::\(O(\log n)\)}}</td> <td>{{c5::\(O(n)\)}}</td> <td>{{c6::\(O(n)\)}}</td> </tr> <tr> <td>DLL</td> <td>{{c7::\(O(n)\) (no bin. search possible)}}</td> <td>{{c8::\(O(1)\)}}</td> <td>{{c9::\(O(n)\)}}</td> </tr> </tbody></table> |
Note 3: ETH::A&D
Note Type: Horvath Cloze
GUID:
n/PBpw~:i9
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | We can use a binary search tree to implement the dictionary. The tree-condition is {{c1::for every node, all keys in the left child are smaller than those in the right child}}. |
Note 4: ETH::A&D
Note Type: Horvath Cloze
GUID:
kR-q@1!eo3
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Runtime: <b>search</b> in binary tree: {{c1::\(O(h)\) where \(h\) is the height}}. |
Note 5: ETH::A&D
Note Type: Horvath Classic
GUID:
tH)JXa7KfA
Previous
Note did not exist
New Note
Front
Back
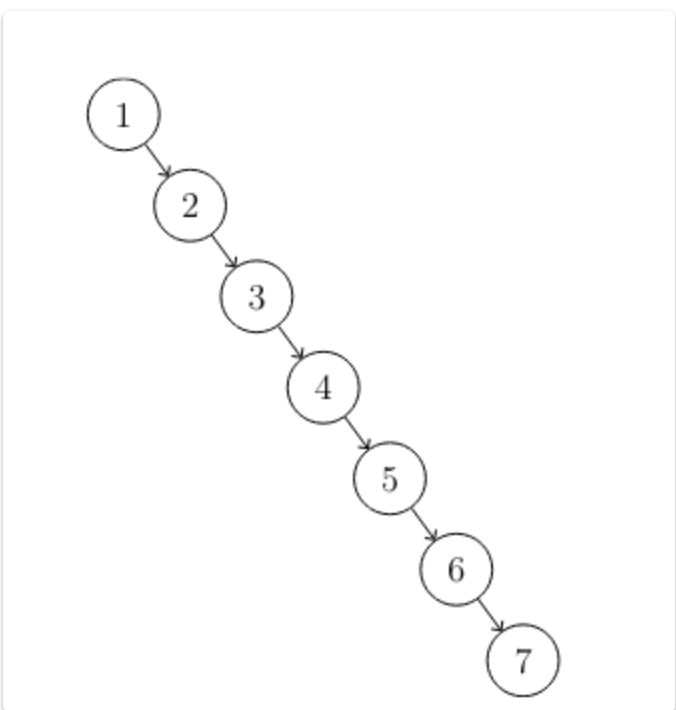
Worst case example if inserted in ascending order:
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | <b>Worst case</b> for <b>search</b> in a <b>binary tree</b>? | |
| Back | Binary trees are not <b>balanced</b> possible that \(h >> \log_2 n\)<br>Worst case example if inserted in ascending order:<br><b></b><img src="paste-201c49e27928e7a814e89e8de667e07e5c7789ce.jpg"> |
Note 6: ETH::A&D
Note Type: Horvath Classic
GUID:
uHC]1fZd$=
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | <b>Tree Condition</b>: for <b>2-3 Trees</b> implementing dictionary. | |
| Back | Each node has <b>2 or 3 children</b> but that all leafs are <b>on the same level</b> |
Note 7: ETH::A&D
Note Type: Horvath Cloze
GUID:
H0^#YREe-o
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | A <b>2-3 Tree</b> is an {{c1:: external}} search-tree. | |
| Extra | This means that the values are stored in the leaves only. The nodes are for "navigation". |
Note 8: ETH::A&D
Note Type: Horvath Classic
GUID:
FYr.:eNxT,
Previous
Note did not exist
New Note
Front
Back
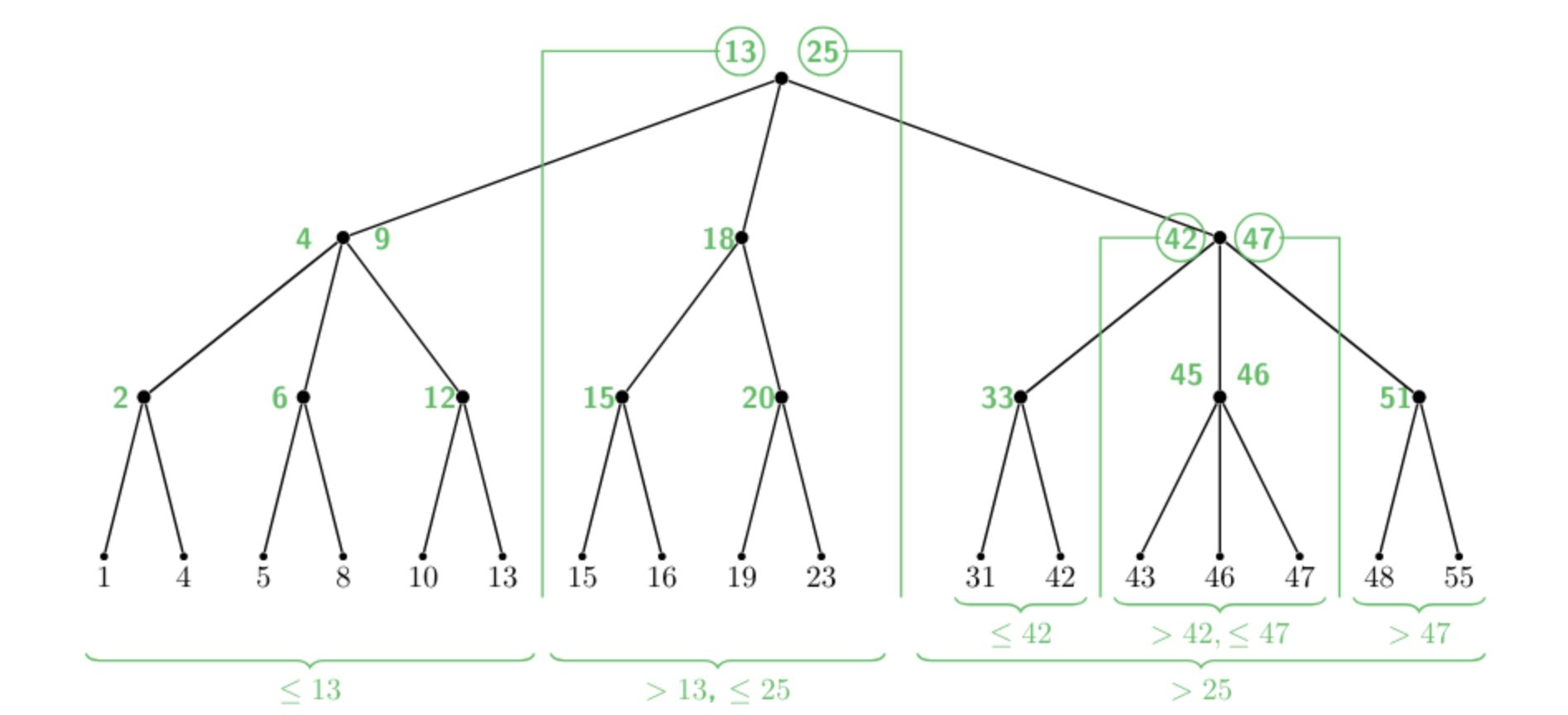
- 2 children: 1 separator \(s\) s.t. for \(l \leq s < r\).
- 3 children: 2 separators \(s_1, s_2\) s.t. \(l \leq s_1 < m \leq s_2 < r\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Types of <b>2-3 Tree</b> nodes: | |
| Back | keys in left (middle, right) sub-tree \(l\) (\(m, r\) respect.ively):<br><ol><li>2 children: 1 separator \(s\) s.t. for \(l \leq s < r\).</li><li>3 children: 2 separators \(s_1, s_2\) s.t. \(l \leq s_1 < m \leq s_2 < r\)</li></ol><img src="paste-099f4518906c93c69e397c80221d3fd5535c17e2.jpg"><br> |
Note 9: ETH::A&D
Note Type: Horvath Cloze
GUID:
wbdb9#fK:J
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Height of a <b>2-3 Tree</b> for \(n\) keys is {{c1::\(\leq \log_2(n)\)}} thus \(h=\){{c2::\(O(\log(n)\)}} (O-notation). | |
| Extra | Note that for the case \(n = 1\) the root has one leaf with the key. |
Note 10: ETH::A&D
Note Type: Horvath Cloze
GUID:
Br&58pkCU{
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | We start counting the height of a tree at {{c1::\(0\)}}. |
Note 11: ETH::A&D
Note Type: Horvath Cloze
GUID:
Bz)mOB:[n-
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <b>2-3 Tree</b>: Runtime of: Search, Inserting, Deleting: {{c1:: \(O(\log n)\)}} | |
| Extra | This is because the tree is now forced to be balanced and \(h \leq \log_2 n\). |
Note 12: ETH::A&D
Note Type: Horvath Cloze
GUID:
H?Cs9sT6&{
Previous
Note did not exist
New Note
Front
- Search for the correct node under which the key is inserted: \(O(\log_2 n)\)
- Insert the new key value as a separator
- Rebalance (if necessary, i.e. more than 3 keys)
- split node into two nodes (each gets 2 children and 1 seps)
- the middle sep is pushed to the parent level (and propagate)
Back
- Search for the correct node under which the key is inserted: \(O(\log_2 n)\)
- Insert the new key value as a separator
- Rebalance (if necessary, i.e. more than 3 keys)
- split node into two nodes (each gets 2 children and 1 seps)
- the middle sep is pushed to the parent level (and propagate)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <b>2-3 Tree</b>: Inserting Steps:<br><ol><li>{{c1::Search for the correct node under which the key is inserted: \(O(\log_2 n)\)}}</li><li>{{c2::Insert the new key value as a <b>separator</b>}}</li><li>{{c3::<b>Rebalance</b> (if necessary, i.e. more than 3 keys)<br></li></ol><ul><li>split node into two nodes (each gets 2 children and 1 seps)</li><li>the middle sep is pushed to the parent level (and propagate)}}</li></ul> | |
| Extra | The rebalancing being recursively pushed to the parent limits the operations at the height \(h\) thus we get \(O(\log n)\). |
Note 13: ETH::A&D
Note Type: Horvath Cloze
GUID:
OY@2Ay+>4p
Previous
Note did not exist
New Note
Front
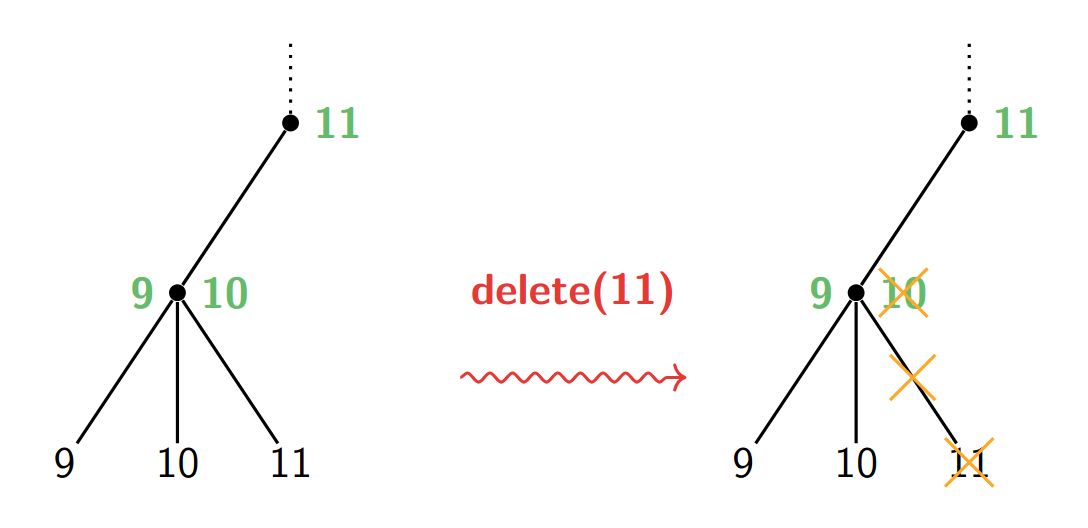
- Search for the correct node under which the key is inserted: \(O(\log_2 n)\)
- Remove the leaf with the value and one separator
- Rebalance (if necessary, i.e. now 1 key)
Back
- Search for the correct node under which the key is inserted: \(O(\log_2 n)\)
- Remove the leaf with the value and one separator
- Rebalance (if necessary, i.e. now 1 key)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <b>2-3 Tree</b>: Deleting Steps:<br><ol><li>{{c1::Search for the correct node under which the key is inserted: \(O(\log_2 n)\)}}</li><li>{{c2::Remove the leaf with the value and one separator}}</li><li>{{c3::<b>Rebalance</b> (if necessary, i.e. now 1 key)}}</li></ol> | |
| Extra | <img src="paste-7d452d931b0485669156a2669de65234617e5eb6.jpg"> |
Note 14: ETH::A&D
Note Type: Horvath Classic
GUID:
m3`Qbb~x?c
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
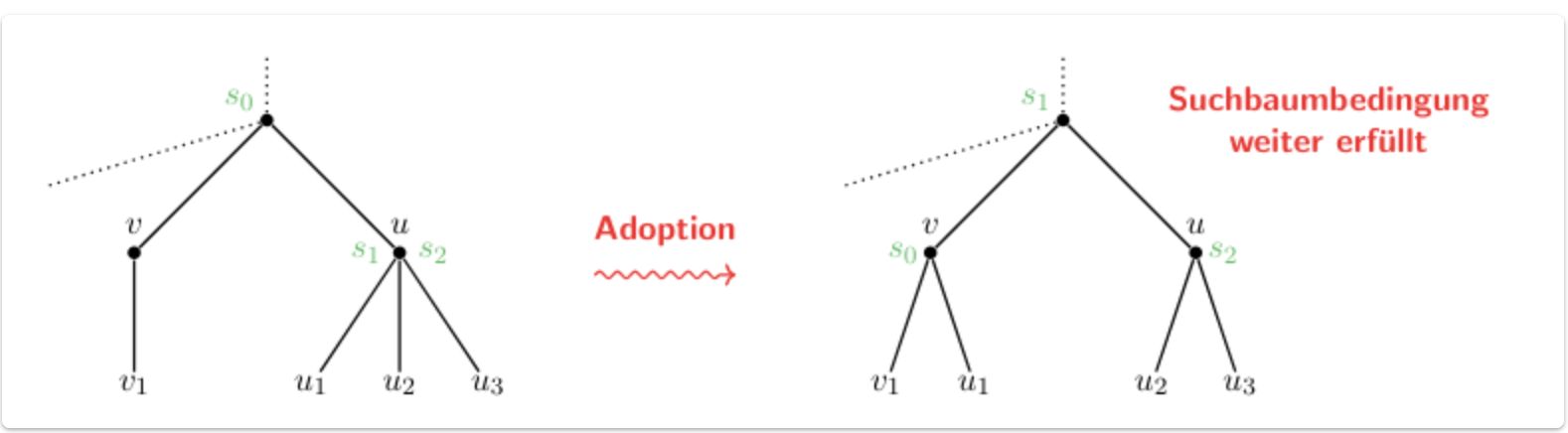
| Front | <b>2-3 Tree</b>: Deleting Steps if neighbour has 3 keys: | |
| Back | Our current node adopts one of the children. The separators have to be updated (one is given with the adopted child)<br><img src="paste-bd8f4c10d3d0aaa08619b4e358673f9ff6b134a0.jpg"> |
Note 15: ETH::A&D
Note Type: Horvath Classic
GUID:
Q}a3<1,J]C
Previous
Note did not exist
New Note
Front
Back
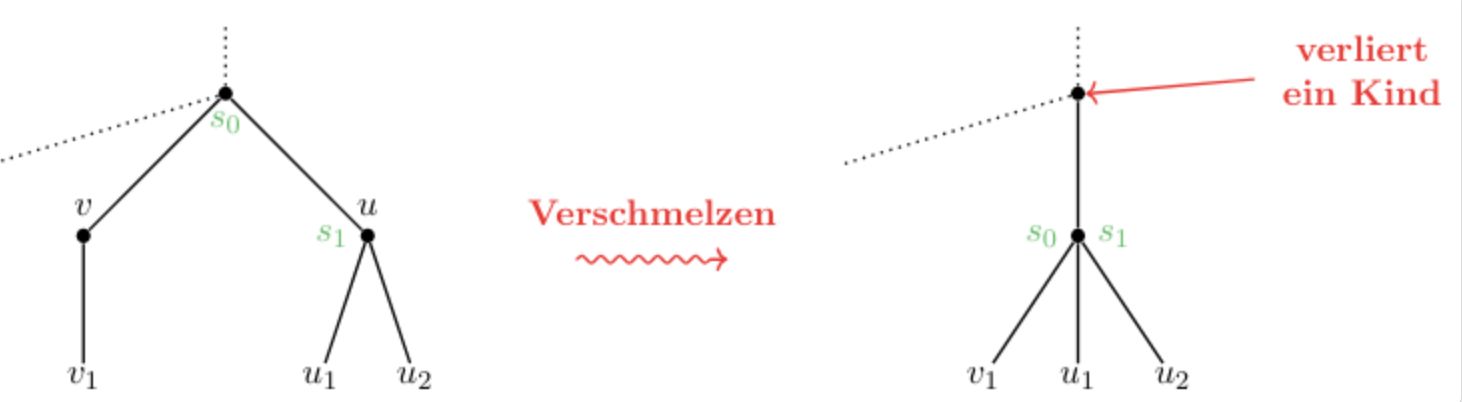
- the nodes \(u\) and \(v\) are merged to form one new node with 3 children.
- The separator from the parent node is pulled down to be the new \(s_2\).
If root has 1 child -> root replaced by child.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | 2-3 Tree: Deleting Steps if neighbour has 2 keys: | |
| Back | <ol><li>the nodes \(u\) and \(v\) are <b>merged</b> to form one new node with <b>3 children</b>.</li><li>The separator from the parent node is pulled down to be the new \(s_2\).</li></ol>Parent may lose child -> rebalance there (can go up to the root).<br>If root has 1 child -> root replaced by child.<br><img src="paste-fcffee6f619138677fc86eb74beebfaa266c8cfe.jpg"> |
Note 16: ETH::A&D
Note Type: Horvath Cloze
GUID:
Q3:!A9V`D,
Previous
Note did not exist
New Note
Front
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of Entry (Base Case, recursive formula, pay attention to bounds!)
- Calculation Order (what depends on what entries, what variable incremented first)
- Extract Solution (How to get final solution out)
- Running time proof
Back
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of Entry (Base Case, recursive formula, pay attention to bounds!)
- Calculation Order (what depends on what entries, what variable incremented first)
- Extract Solution (How to get final solution out)
- Running time proof
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Steps of giving a DP solution:<br><ol><li>{{c1::Define the DP table (dimensions, index, range; meaning of entry): ex: <b>DP[1..n+1][1..k+1]</b>}}</li><li>{{c2::Computation of Entry (Base Case, recursive formula, pay attention to bounds!)}}</li><li>{{c3::Calculation Order (what depends on what entries, what variable incremented first)}}</li><li>{{c4::Extract Solution (How to get final solution out)}}</li><li>{{c5::Running time proof}}</li></ol> | |
| Extra | SMIROST (Size, Meaning, Initialisation, Recursive, Order, Solution, Time) |
Note 17: ETH::A&D
Note Type: Horvath Classic
GUID:
vgCb-fRsjm
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Runtime from DP Table | |
| Back | We use the number of entries * the time to compute them (usually \(O(1)\)) |
Note 18: ETH::A&D
Note Type: Horvath Cloze
GUID:
J!K^!6M$e^
Previous
Note did not exist
New Note
Front
- subarray: continous partition of the original
- subsequence: non-continous partition
- subset any subset (order does not matter)
Back
- subarray: continous partition of the original
- subsequence: non-continous partition
- subset any subset (order does not matter)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Differences between Subarray vs. Subsequence vs. Subset:<br><ul><li><b>subarray</b>: {{c1:: continous partition of the original}}</li><li><b>subsequence</b>: {{c2:: non-continous partition}}</li><li><b>subset</b> {{c3:: any subset (order does not matter)}}</li></ul> |
Note 19: ETH::A&D
Note Type: Algorithms
GUID:
rUd4]Y&$Fr
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Maximum Subarray Sum | |
| Runtime | \(\Theta(n)\) | |
| Approach | Table: DP[1..n]<br>Define the "randmax": \( R_j := \max_{1 \leq i \leq j} \sum_{k = i}^j A[k] \) (maximale summe eines teilarrays das an j endet.<br><ul><li>Base Case: \(R_1 = A[1]\)</li><li>Recursion is \(R_j = \max \{ A[j], R_{j - 1} + A[j] \}\)<br>Thus either our current subarray contains the element at j, or not and we start with it again.</li></ul> | |
| Pseudocode | <img src="paste-8b50441eb44313fbab2c817e37ae70bb89ab0449.jpg"> |
Note 20: ETH::A&D
Note Type: Algorithms
GUID:
tYh57HT9#t
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Jump Game | |
| Runtime | \(O(n)\) (hyper-optimised version) | |
| Requirements | Minimal jumps to get from beginning of array to the end.<br><br>Variable switch: cells which we can reach in \(k\) jumps. Solution is smallest \(k\) for which \(M[k] \geq n\).<br><br>We look at all \(i\) we can reach with exactly \(k-1\) jumps:<br><ul><li>Base Case: \(M[0] = A[0]\), \(M[1] = A[1] + 1\)</li><li>Recursion: \( M[k] = \max \{i + A[i] \ | \ M[k - 2] \leq i \leq M[k - 1]\} \)</li></ul><div>We look exactly 1 at every \(i\), thus \(O(n)\)</div> | |
| Pseudocode | <img src="paste-1f13db1cbb6b8d772fa2de2563b63627af8a038f.jpg"> |
Note 21: ETH::A&D
Note Type: Horvath Reverso
GUID:
l2vPmFwTj!
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Subsequence | |
| Back | Teilfolge |
Note 22: ETH::A&D
Note Type: Algorithms
GUID:
o-3hRLI()p
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
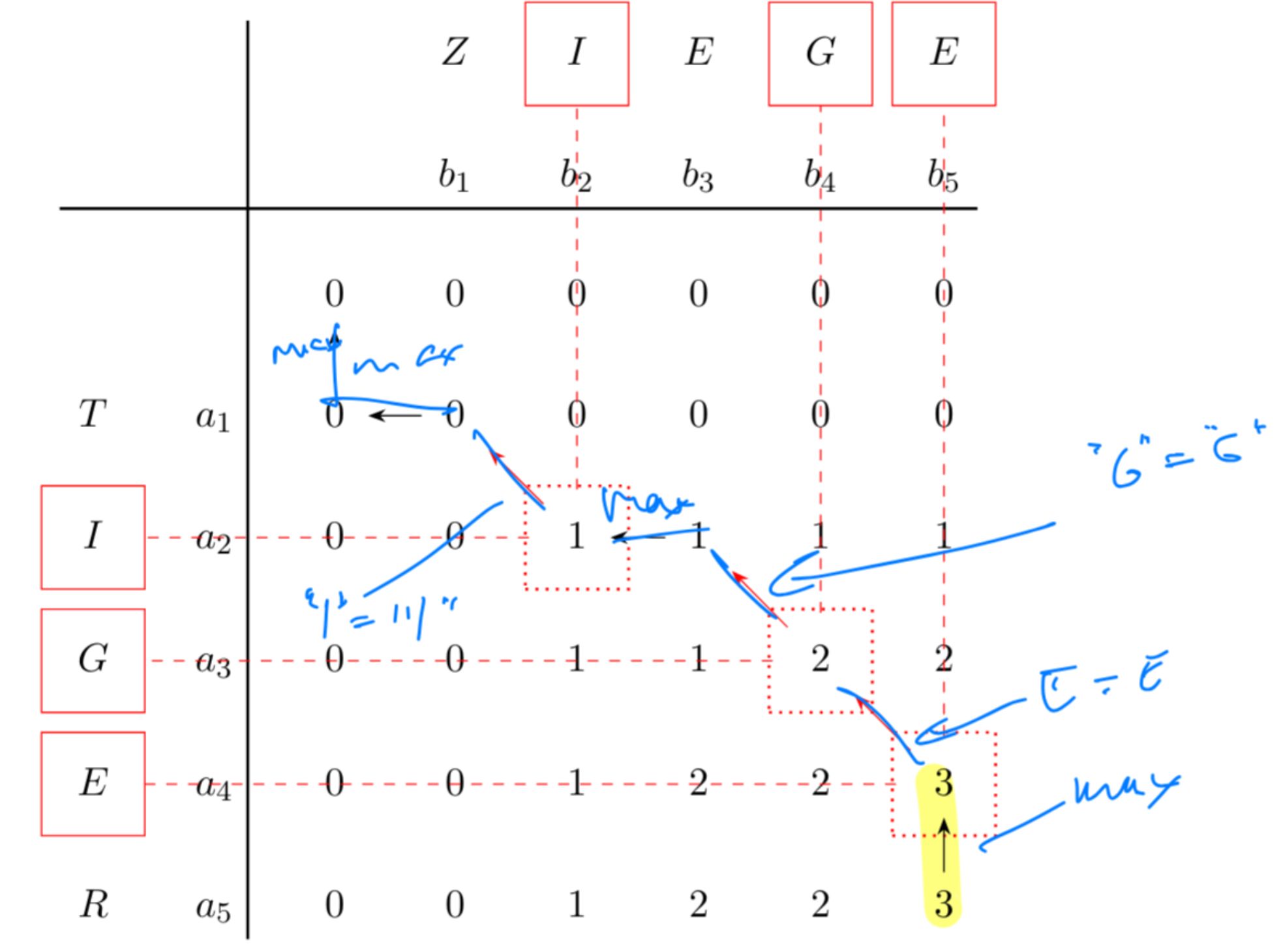
| Name | Longest Common Subsequence | |
| Runtime | \(\Theta(n \cdot m)\) | |
| Approach | <div>DP-Table: <code>DP[0..n][0..m]</code> for \(n, m\) lengths of the strings</div><div><br></div><div><div>longest common subsequence that two strings share. For example TIGER and ZIEGE share IGE as a LGT.</div></div><div><br></div><div> <div>This gives us the following recursion: \[L(i,j) = \begin{cases} 0, & i = 0 \text{ oder } j = 0 \\ L(i-1, j-1) + 1, & X_i = Y_j \\ \max(L(i-1,j), L(i,j-1)), & X_i \neq Y_j \end{cases}\]</div></div> | |
| Pseudocode | <img src="paste-5d0d1e2b1030b40ef6fce29f1fe1bd0e71105b03.jpg"> |
Note 23: ETH::A&D
Note Type: Horvath Classic
GUID:
i~[|jYI|rt
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Backtracking in DP Problems | |
| Back | Backtracking can find the solution of the problem from the DP table. From the recursion and it's behaviour we find the "path"<br><br><img src="paste-c186a33203c3cb874cfeb7870ee1a4c5d52bf205.jpg"> |
Note 24: ETH::A&D
Note Type: Algorithms
GUID:
gE_4/z}oud
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Editing Distance | |
| Runtime | \(\Theta(n \cdot m)\) | |
| Approach | Minimum amount of edits (insert, delete, replace) to go from s1 to s2 -> LGT gives us the ED.<br><br>Three cases for \(a_i\) last char of \(a\):<br><ul><li>deleted: \(ED(i, j) = 1 + ED(i - 1, j)\) (if deleted, it doesn't matter when)<br><img src="paste-254e45a17676954472f6aebe7c8c4f0517b3d6b5.jpg"></li><li>ends up in \(1, \dots, j-1\): no char \(a_k, k < i\) can be behind \(a_i\) (suboptimal as it would cost 2): \(E1+ ED(i, j -1)\)<br><img src="paste-fae70ea53a12531dc9ac1ac30b00512b6f0c150e.jpg"></li><li>ends up at \(b_j\): cannot insert char behind \(a_i\) thus: \(ED(i-1, j -1) \) if \(a_i = b_j\) else \(1 + ED(i-1, k-1)\) <br><img src="paste-3027dc66600e0cb2f8e3a1b12c8a1be248f13f5c.jpg"> </li></ul> | |
| Pseudocode | <img src="paste-1a255e78854ef70231b746a53228cd5420abeee8.jpg"> |
Note 25: ETH::A&D
Note Type: Algorithms
GUID:
L`3Iw:nx:Z
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Subset Sum (Teilsummenproblem) | |
| Runtime | \(\Theta(n \cdot b)\) (Pseudo-Polynomial) | |
| Requirements | We want to find the subset \(I \subseteq \{1, \dots, n\}\) such that \(\sum_{i \in I} A[i] = b\) (must not exist for all \(b\)).<br><br>\(T(i,s)\) is 1 if there exists a subset from 1 to i that sums to s<br><ul><li>Base Case: T(0, 0) = 1 as we can use </li><li>Recursion: \( T(i, s) = T(i - 1, s) \ \lor \ T(i - 1, s - A[i]) \)</li></ul><div>Either we use A[i] or we don't.</div> |
Note 26: ETH::A&D
Note Type: Algorithms
GUID:
L~wgr~ELJV
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Knapsack Problem (Rucksackproblem) | |
| Runtime | \(\Theta(n\cdot W)\) or \(\Theta(n \cdot P)\) (Pseudopolynomial) | |
| Approach | Subset problem choosing the maximum staying under a weight \(W\).<br>The greedy algorithm fails as a local optimum is not global here.<br><br>Base Cases: \(dp[0][w] = 0, \quad dp[i][0] = 0\)<br>If item weight > max allowed left, don't take it. Otherwise get the max from using it or not:<br>\(dp[i][w] = \begin{cases} dp[i-1][w], & w_i > w \\ \max(dp[i-1][w], dp[i-1][w-w_i] + v_i), & \text{sonst} \end{cases}\) | |
| Pseudocode | <img src="paste-dfd5963f4f4fabfa2ea13e840d1530b8d7fe1a4a.jpg"> |
Note 27: ETH::A&D
Note Type: Horvath Classic
GUID:
o>e0u7Qnuv
Previous
Note did not exist
New Note
Front
Back
The DP-table get's 10x for \(W = 10 \rightarrow 100\) but the input size (binary) only grows from \(\log_2(10) \approx 3 \rightarrow \approx 6\) so x2.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | What is pseudo-polynomial time? | |
| Back | runtime dependent on a number \(W\) (like in knapsack) which is not correlated polynomially to input length but exponentially.<br><br>The DP-table get's 10x for \(W = 10 \rightarrow 100\) but the input size (binary) only grows from \(\log_2(10) \approx 3 \rightarrow \approx 6\) so x2. |
Note 28: ETH::A&D
Note Type: Horvath Classic
GUID:
pK&d|%vUW(
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | How can we make Knapsack polynomial using approximation? | |
| Back | round the profits and solve the Knapsack problem for these rounded profits:\(\overline{p_i} := K \cdot \lfloor \frac{p_i}{K} \rfloor\). We then only have to compute every K'th entry to the DP-table. |
Note 29: ETH::A&D
Note Type: Algorithms
GUID:
C$#TvbwG_l
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Longest Ascending Subsequence (Längste Aufsteigende Teilfolge) | |
| Runtime | \(\Theta(n \log n)\) | |
| Approach | For an array A[1..n] <b>longest</b> subsequence (non-continuous) that is ascending.<br><br>DP Table with entry \(M(l) = a\) where a ist the smallest possible ending of a LAT with length \(l\).<br><ul><li>Base Cases: \(M[*] = \infty\)</li><li>Recursion: set \(M[k]\) to \(A[i]\) where \(k\) is the index of the next smallest + 1 in \(M\).</li></ul>We can find the smaller with binary search, thus \(\log n \) search for \(n\) elements -> \(\Theta(n \log n)\).<br><img src="paste-1b9069bf0a881a3cd3900a4de699cac89f0498b8.jpg"><br> | |
| Pseudocode | <img src="paste-0cd3692a4a909acf7f7ae0540eb6d714fc346b41.jpg"> |
Note 30: ETH::A&D
Note Type: Horvath Cloze
GUID:
QJ{Y%?s>+w
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | When writing the recursion, make sure that if the index {{c1:: goes out of bound, you specify the "neutral"}}. | |
| Extra | For subset sum, we take \(DP[i-1][B - b_i]\), where if we don't check \(B - b_i\) might go negative and thus oob. |
Note 31: ETH::A&D
Note Type: Horvath Classic
GUID:
w{Q]%!`f&#
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Transform Eulerian walk to closed eulerian walk problem: | |
| Back | add an edge connected the start-end points with odd degrees. |
Note 32: ETH::A&D
Note Type: Algorithms
GUID:
AJT5T7qaW3
Previous
Note did not exist
New Note
Front
Back
In an Adjacency Matrix: runtime is \(O(n^2)\) as looping over all edges is \(O(n)\).
In an Adjacency List: we loop \(n\) times over \(O(1 + \deg(u))\).
Using the handshake lemma: \(\sum_{u \in V} (1 + \deg(u)) = n + \sum_{u \in V} \deg(u) = n + 2m\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Name | Find Closed Eulerian Path | |
| Runtime | \(O(n+m)\) | |
| Approach | We want to be able to find closed walks in a graph. We can then merge them together to form a single closed walk, by exploiting shared vertices.<br><br>Algo:<br><ol><li>Start at vertex \(u_0\) arbitrary</li><li>For loop over edges. If not marked, mark and recurse.</li><li>Append vertex to list after execution</li></ol> Returns a list of vertices in order of a closed walk if there is one.<br><br>Example:<br><img src="paste-a669de30c7bc4a38d788fb96b6b5551a4781ec71.jpg"><br>Output:<br><img src="paste-b453826818903aa4da2ac10897e9dc0e177229b6.jpg"> | |
| Pseudocode | <img src="paste-b2cbbb1cb599a09a77bcc0e991ec4bcb83c586fb.jpg"><br><img src="paste-c82a6519899f9b1f1f49c932a2b252ff64a2184a.jpg"> | |
| Extra Info | In an Adjacency Matrix: runtime is \(O(n^2)\) as looping over all edges is \(O(n)\).<br><br>In an Adjacency List: we loop \(n\) times over \(O(1 + \deg(u))\).<br>Using the handshake lemma: \(\sum_{u \in V} (1 + \deg(u)) = n + \sum_{u \in V} \deg(u) = n + 2m\) |
Note 33: ETH::A&D
Note Type: Horvath Cloze
GUID:
mLAF6cI?#i
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Runtime of initialising an adjacency list: {{c1:: \(O(n + m)\)}}. |
Note 34: ETH::A&D
Note Type: Horvath Cloze
GUID:
qYjlu[L8wY
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Runtime of initialising an adjacency matrix: {{c1:: \(O(n^2)\)}}. |
Note 35: ETH::A&D
Note Type: Horvath Cloze
GUID:
p{21Af5^Ae
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | If a vertex of degree \(\geq 2\) is <b>not</b> a cut vertex then {{c1::it must lie on a cycle}}. |
Note 36: ETH::A&D
Note Type: Horvath Cloze
GUID:
s@rY_v*&u_
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | A graph is bipartite if and only if {{c1::it does not contain any cycles of odd length}}. |
Note 37: ETH::A&D
Note Type: Horvath Classic
GUID:
AqQ}Ty8GRj
Previous
Note did not exist
New Note
Front
Back
Median of medians algo ideal but too complex to implement.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | How do we fix the Quicksort worst-case runtime? | |
| Back | Chose a random element as the pivot.<br><br>Median of medians algo ideal but too complex to implement. |
Note 38: ETH::A&D
Note Type: Horvath Cloze
GUID:
ub(U6EB=d{
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | A topological ordering of vertices is an order such that for every edge \((u, v) \), {{c1::\(u\) comes before \(v\)}}. | |
| Extra | thus all arrows point rightwards. |
Note 39: ETH::A&D
Note Type: Horvath Cloze
GUID:
dYrUA*(KY7
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | {{c1:: \(\exists\) toposort}} \(\Longleftrightarrow\) {{c2:: \(\lnot \exists\) directed closed walk}} |
Note 40: ETH::A&D
Note Type: Algorithms
GUID:
kn@H8`z>0t
Previous
Note did not exist
New Note
Front
Back
Can be efficiently implemented using a stack.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
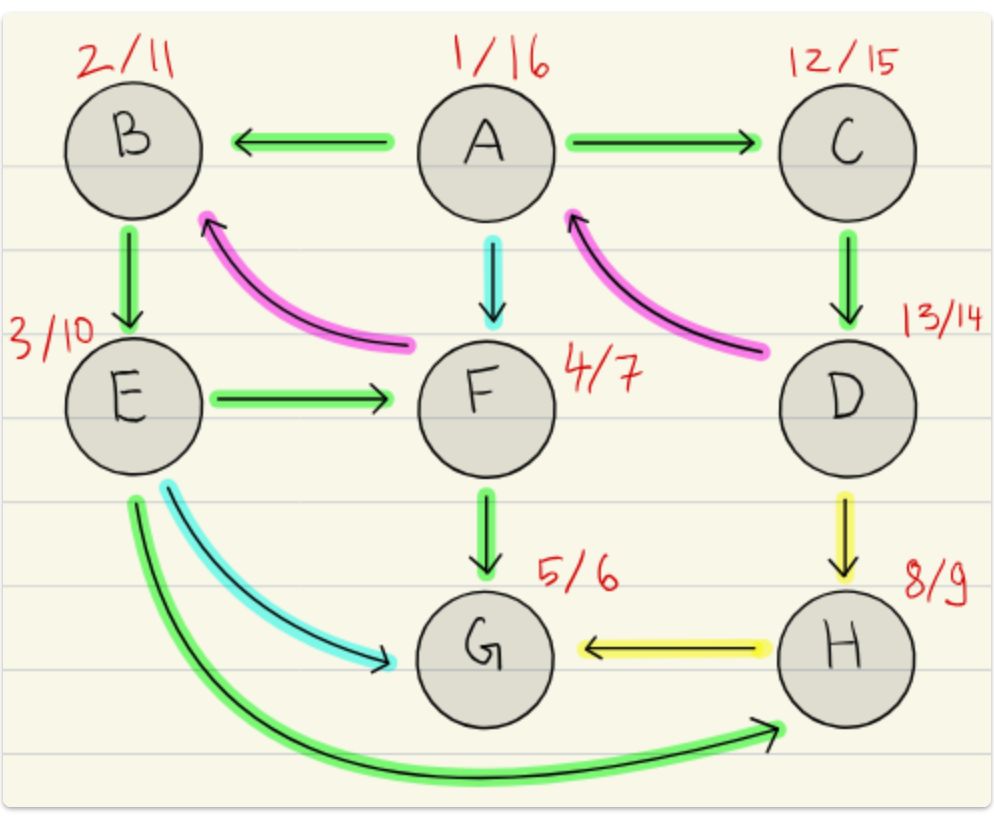
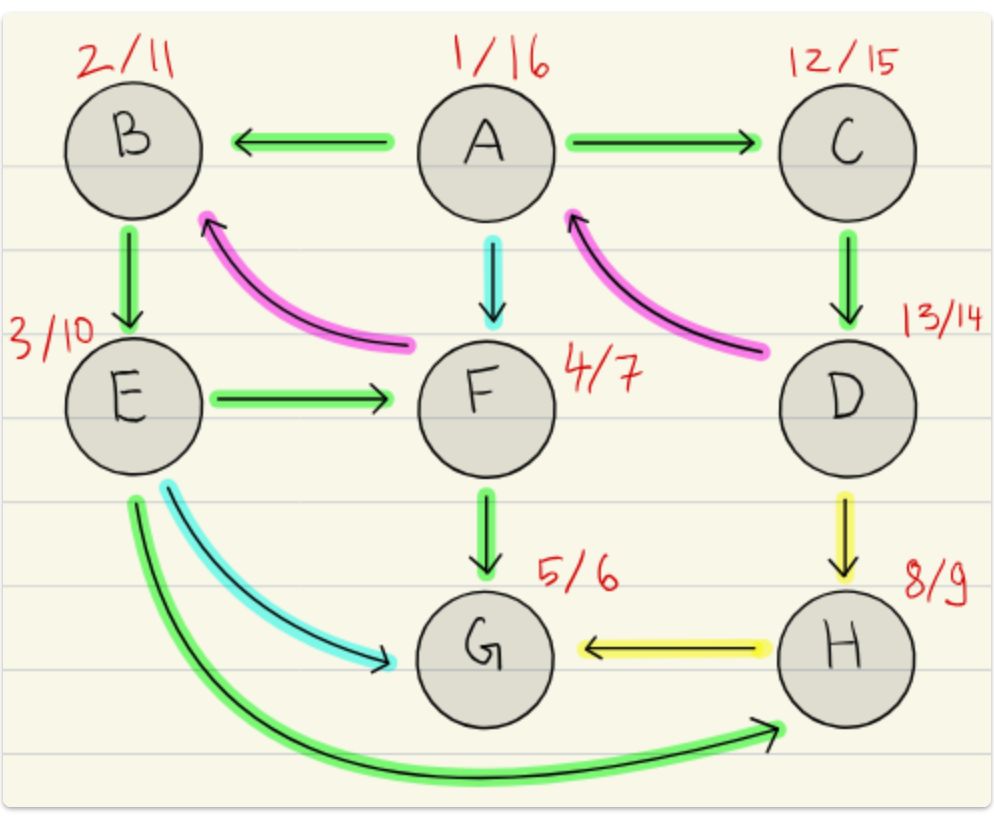
| Name | DFS (Depth First Search) | |
| Runtime | \( \mathcal{O}(|E| + |V|) \) (using Adjacency List) | |
| Approach | Explore as far as possible along each branch before backtracking. Potentially keep track of pre- / post-numbers to make edge classifications.<br><br>We want to find a sink, add it to the list, then backtrack and find the next one.<br><br>The reversed post-order then gives us a toposort.<br><br>Example output:<br><img src="paste-f6163ccea9c72dbfdc9cb9045b600a5a41b8aa6b.jpg"> | |
| Pseudocode | <img src="paste-60a95ac959791d67c7cee55696da90ab82b8f713.jpg"><br><img src="paste-91ab7e22fbe20ca71b32e8db34b737d2c9366c23.jpg"> | |
| Extra Info | Can be efficiently implemented using a stack. |
Note 41: ETH::A&D
Note Type: Horvath Cloze
GUID:
bD%.s|4?hI
Previous
Note did not exist
New Note
Front
\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\): tree edge, as \(v\) is a descendant of \(u\)
Back
\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\): tree edge, as \(v\) is a descendant of \(u\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Pre-/Post-Ordering Classification for an edge \((u, v)\):<br>\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\): {{c1:: tree edge, as \(v\) is a descendant of \(u\)}} |
Note 42: ETH::A&D
Note Type: Horvath Cloze
GUID:
rnACRB4[8n
Previous
Note did not exist
New Note
Front
\(\text{pre}(v) < \text{pre}(u) < \text{post}(u) < \text{post}(v)\): back edge
Back
\(\text{pre}(v) < \text{pre}(u) < \text{post}(u) < \text{post}(v)\): back edge
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Pre-/Post-Ordering Classification for an edge \((u, v)\):<br>\(\text{pre}(v) < \text{pre}(u) < \text{post}(u) < \text{post}(v)\): {{c1:: back edge}} | |
| Extra | exists a cycle! |
Note 43: ETH::A&D
Note Type: Horvath Cloze
GUID:
Auw]yKf@xT
Previous
Note did not exist
New Note
Front
\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\), but not tree edge: Forward edge
Back
\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\), but not tree edge: Forward edge
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Pre-/Post-Ordering Classification for an edge \((u, v)\):<br>\(\text{pre}(u) < \text{pre}(v) < \text{post}(v) < \text{post}(u)\), but <b>not tree edge</b>: {{c1:: Forward edge}} |
Note 44: ETH::A&D
Note Type: Horvath Cloze
GUID:
Bb-m%-jtI|
Previous
Note did not exist
New Note
Front
\(\text{pre}(v) < \text{post}(v) < \text{pre}(u) < \text{post}(u)\): Cross edge, \(u, v\) in different subtrees
Back
\(\text{pre}(v) < \text{post}(v) < \text{pre}(u) < \text{post}(u)\): Cross edge, \(u, v\) in different subtrees
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Pre-/Post-Ordering Classification for an edge \((u, v)\):<br>\(\text{pre}(v) < \text{post}(v) < \text{pre}(u) < \text{post}(u)\): {{c1:: Cross edge, \(u, v\) in different subtrees}} |
Note 45: ETH::A&D
Note Type: Image Occlusion
GUID:
EE{ugGOkjL
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Occlusion | {{c3::image-occlusion:rect:left=.1725:top=.5468:angle=985:width=.3135:height=.1117:oi=1}}<br>{{c1::image-occlusion:rect:left=.1923:top=.2416:width=.2286:height=.2:oi=1}}<br>{{c2::image-occlusion:rect:left=.5726:top=.7584:width=.2179:height=.0701:oi=1}}<br>{{c0::image-occlusion:text:left=.2051:top=.0987:text=B<-F:scale=1.:fs=.1133:oi=1}}<br>{{c0::image-occlusion:text:left=.6132:top=.8338:text=G<-H:scale=.5385:fs=.1133:oi=1}}<br>{{c0::image-occlusion:text:left=.1645:top=.7065:angle=989:text=E->G:scale=.6858:fs=.1133:oi=1}}<br> | |
| Image | <img src="paste-92fb45dcbaee894af9f32d9c2de935b1985dd979.jpg"> |
Note 46: ETH::A&D
Note Type: Horvath Cloze
GUID:
O%OM.97hp$
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | {{c1::\(\exists\) back edge}} \(\Longleftrightarrow\){{c2::\(\exists\) Directed closed walk}} |
Note 47: ETH::A&D
Note Type: Horvath Cloze
GUID:
f2x>M=+L9d
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | \(\forall\) not back-edge \((u,v) \in E\), \( \text{post}(u)\) {{c1::\(\geq\)}} \(\text{post}(v) \) |
Note 48: ETH::A&D
Note Type: Horvath Classic
GUID:
NR^|^~o+xa
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | How do we get the topo sort from DFS? | |
| Back | Reversed Post order |
Note 49: ETH::A&D
Note Type: Horvath Cloze
GUID:
IE=7&p8[(7
Previous
Note did not exist
New Note
Front
- back-edges = forward-edges
- cross edges are not possible
Back
- back-edges = forward-edges
- cross edges are not possible
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | In an undirected graph, what is special about pre/post-ordering:<br><ul><li><div>{{c2::back-edges = forward-edges}}</div></li><li><div><div>cross edges {{c1::are not possible}}</div></div></li></ul> |
Note 50: ETH::A&D
Note Type: Horvath Cloze
GUID:
AY}!l[d)1z
Previous
Note did not exist
New Note
Front
- Overlapping but not Nested Intervals:
- {{c2:: \(\text{pre}(u)<\text{pre}(v)<\text{post}(u)<\text{post}(v)\):
 as visit(u) would call visit(v) before the recursive call ends}}
as visit(u) would call visit(v) before the recursive call ends}}
Back
- Overlapping but not Nested Intervals:
- {{c2:: \(\text{pre}(u)<\text{pre}(v)<\text{post}(u)<\text{post}(v)\):
 as visit(u) would call visit(v) before the recursive call ends}}
as visit(u) would call visit(v) before the recursive call ends}}
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Name the impossible cases in DFS pre/post ordering for edge \((u, v)\):<br><ul><li>{{c1::Overlapping but not Nested Intervals: <img src="paste-b7976dbbff12de2b44594553e0c91633f59e9c05.jpg">}}</li><li>{{c2:: \(\text{pre}(u)<\text{pre}(v)<\text{post}(u)<\text{post}(v)\): <img src="paste-a6fc070f96de8bd2b8148e3891cf956fd611a0a2.jpg"> as visit(u) would call visit(v) before the recursive call ends}}</li></ul> |
Note 51: ETH::A&D
Note Type: Horvath Classic
GUID:
QBdl=YAmG|
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Check for cycles in DFS algo: | |
| Back | During the recursive call, if we find an adjacent vertex <b>without a post-number</b>, there's a back-edge (\(\implies\)the recursive call for that edge is still active...) |
Note 52: ETH::A&D
Note Type: Horvath Classic
GUID:
v7@jgp_hjT
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Find cross edge in DFS algorithm: | |
| Back | If we find vertex with both pre- and post- there's a cross edge. |
Note 53: ETH::A&D
Note Type: Horvath Classic
GUID:
gCxT2!W2sa
Previous
Note did not exist
New Note
Front
Back
- Matrix: \(O(n)\) as we loop edges gives \(n \cdot O(n) = O(n^2)\)
- List: \(O(1 + \deg_{out}(u))\) gives \(n \cdot O(1 + \deg_{out}(v) = |V| + |E|\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Runtime of DFS with matrix vs list: | |
| Back | \(n\) calls to visit. Each takes:<br><ul><li>Matrix: \(O(n)\) as we loop edges gives \(n \cdot O(n) = O(n^2)\)</li><li>List: \(O(1 + \deg_{out}(u))\) gives \(n \cdot O(1 + \deg_{out}(v) = |V| + |E|\)</li></ul> |
Note 54: ETH::A&D
Note Type: Horvath Classic
GUID:
nzhNF&3(!D
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Handshake lemma in directed graphs: | |
| Back | \[ \sum_{v \in V} \deg_{out}(v) = \sum_{v \in V} \deg_{in}(v) = |E| \]<br> |
Note 55: ETH::A&D
Note Type: Horvath Cloze
GUID:
GA*(aETcmb
Previous
Note did not exist
New Note
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | DFS Runtime: In a sparse graph {{c1:: adjacency list better}}, in a dense graph {{c1:: adjacency matrix is better}}. | |
| Extra | \(|E| \geq |V|^2 / 10\), then DFS has the same runtime in the worst-case using adjacency matrices or lists as \(|V| + |E| \leq |V| + |V|^2 \)which is \(O(n^2)\). |