- subarray: continous partition of the original
- subsequence: non-continous partition
- subset any subset (order does not matter)
Note 1: ETH::A&D
Note Type: Image Occlusion-73a2c
GUID:
GKG~Tp?e4l
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Occlusion | {{c |
{{c5::image-occlusion:rect:left=.592:top=.4403:width=.0786:height=.0963:oi=1}}<br>{{c10::image-occlusion:rect:left=.5847:top=.571:width=.0859:height=.0963:oi=1}}<br>{{c12::image-occlusion:rect:left=.444:top=.6983:width=.0786:height=.0963:oi=1}}<br>{{c3::image-occlusion:rect:left=.7912:top=.313:width=.0859:height=.1101:oi=1}}<br>{{c2::image-occlusion:rect:left=.5884:top=.313:width=.0822:height=.1032:oi=1}}<br>{{c11::image-occlusion:rect:left=.4404:top=.5641:width=.0932:height=.1032:oi=1}}<br>{{c7::image-occlusion:rect:left=.7912:top=.5779:width=.0859:height=.0894:oi=1}}<br>{{c1::image-occlusion:rect:left=.4367:top=.3061:width=.0895:height=.117:oi=1}}<br>{{c4::image-occlusion:rect:left=.4367:top=.4472:width=.0895:height=.0963:oi=1}}<br>{{c8::image-occlusion:rect:left=.7839:top=.6983:width=.0968:height=.0963:oi=1}}<br>{{c9::image-occlusion:rect:left=.5879:top=.6944:width=.0749:height=.1042:oi=1}}<br>{{c6::image-occlusion:rect:left=.7912:top=.4403:width=.0822:height=.1101:oi=1}}<br> |
Note 2: ETH::A&D
Note Type: Horvath Cloze
GUID:
J!K^!6M$e^
Before
Front
Back
- subarray: continous partition of the original
- subsequence: non-continous partition
- subset any subset (order does not matter)
After
Front
- Subarray: continous partition of the original
- Subsequence: non-continous partition
- Subset: any subset (order does not matter)
Back
- Subarray: continous partition of the original
- Subsequence: non-continous partition
- Subset: any subset (order does not matter)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Differences between Subarray vs. Subsequence vs. Subset:<br><ul><li><b> |
Differences between Subarray vs. Subsequence vs. Subset:<br><ul><li><b>Subarray</b>: {{c1:: continous partition of the original}}</li><li><b>Subsequence</b>: {{c2:: non-continous partition}}</li><li><b>Subset:</b> {{c3:: any subset (order does not matter)}}</li></ul> |
Note 3: ETH::A&D
Note Type: Horvath Cloze
GUID:
M11/nZaHIu
Before
Front
| search | insert | delete | |
| unsorted Array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| sorted Array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| DLL | \(O(n)\) (no bin. search possible) | \(O(1)\) | \(O(n)\) |
Back
| search | insert | delete | |
| unsorted Array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| sorted Array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| DLL | \(O(n)\) (no bin. search possible) | \(O(1)\) | \(O(n)\) |
After
Front
| Search | Insertion | Deletion | |
| Non-sorted array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| Sorted array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| Doubly linked list | \(O(n)\) | \(O(1)\) | \(O(n)\) |
Back
| Search | Insertion | Deletion | |
| Non-sorted array | \(O(n)\) | \(O(1)\) | \(O(n)\) |
| Sorted array | \(O(\log n)\) | \(O(n)\) | \(O(n)\) |
| Doubly linked list | \(O(n)\) | \(O(1)\) | \(O(n)\) |
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <b></b><b></b><b></b><b></b><table>
<tbody><tr>
<td></td>
<td><b> |
<b></b><b></b><b></b><b></b><table> <tbody><tr> <td></td> <td><b>Search</b></td> <td><b>Insertion </b></td> <td><b>Deletion</b></td> </tr> <tr> <td>Non-sorted array </td> <td>{{c1::\(O(n)\)}}</td> <td>{{c2::\(O(1)\)}}</td> <td>{{c3::\(O(n)\)}}</td> </tr> <tr> <td>Sorted array</td> <td>{{c4::\(O(\log n)\)}} </td> <td>{{c5::\(O(n)\)}}</td> <td>{{c6::\(O(n)\)}}</td> </tr> <tr> <td>Doubly linked list </td> <td>{{c7::\(O(n)\)}}</td> <td>{{c8::\(O(1)\)}}</td> <td>{{c9::\(O(n)\)}}</td> </tr> </tbody></table> |
Note 4: ETH::A&D
Note Type: Algorithms
GUID:
NAHrkHd^ik
Before
Front
Back
Worst Case: \(O(n \log n)\)
After
Front
Back
Worst Case: \(O(n \log n)\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Attributes | Not in place, thus the space complexity is \(K(n)\). (Though it can be implemented as such)<br><b>Stable</b> |
Note 5: ETH::A&D
Note Type: Horvath Cloze
GUID:
Pf|C9|^n[w
Before
Front
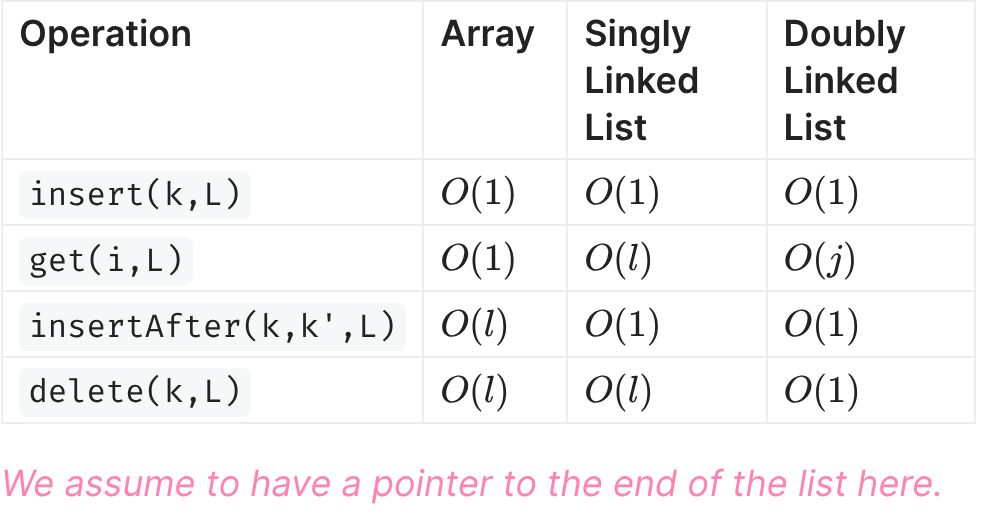
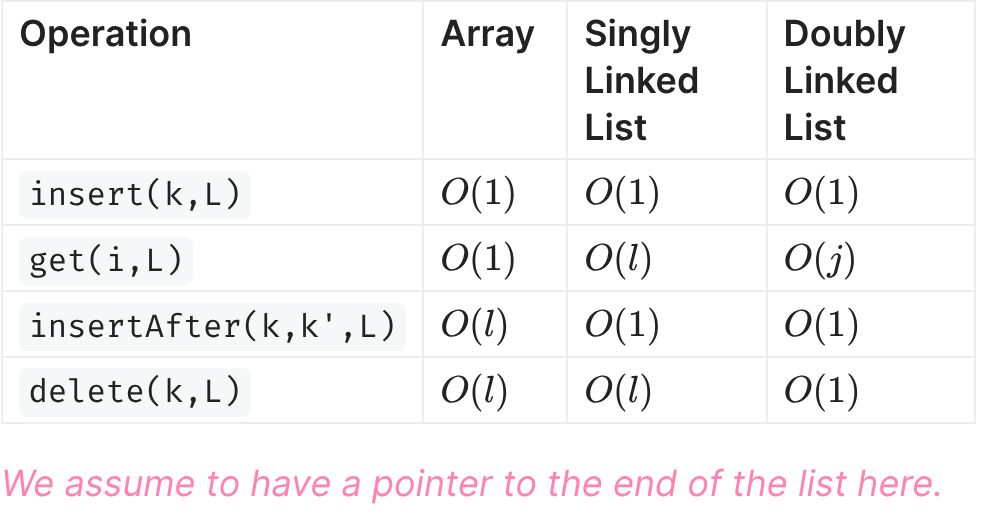
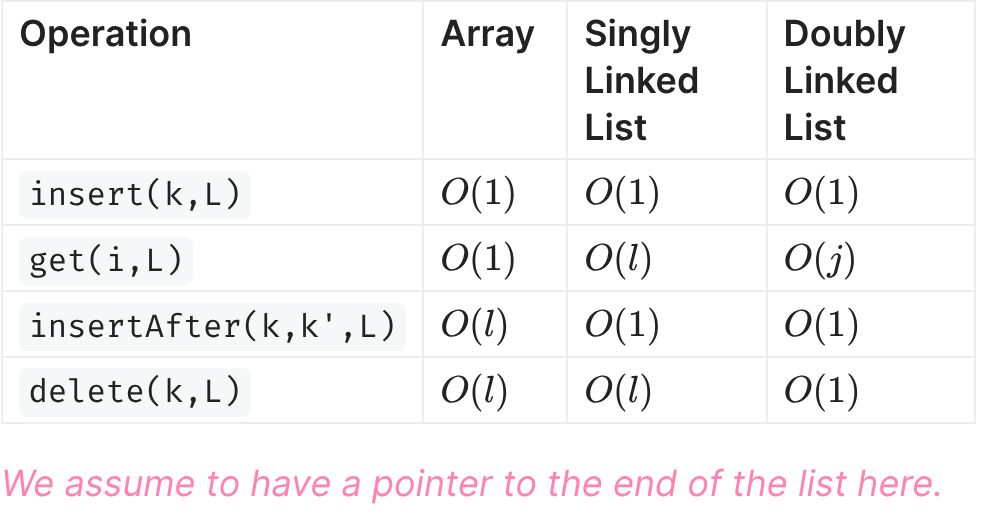
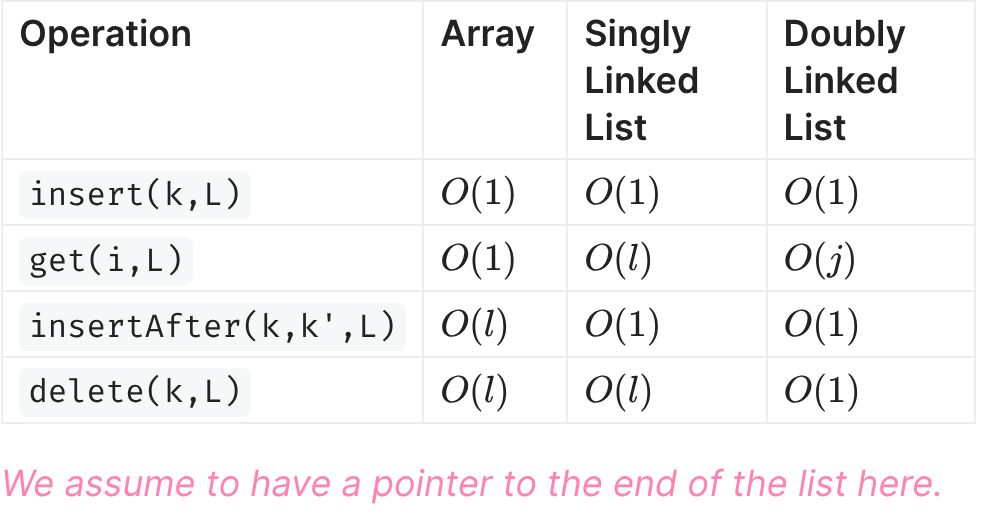
- Insert is \(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\).
- Get is \(\Theta(i)\) very slow as we need to traverse the entire list up to i
- insertAfter is \(O(1)\) if we get the memory address of the element to insert after.
- delete is:
SLL: {{c4::\(\Theta(l)\) as we need to find the previous element and change it's pointer}.}
DLL: \(O(1)\) we know the address of the previous element and then just edit it's pointer.
Back
- Insert is \(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\).
- Get is \(\Theta(i)\) very slow as we need to traverse the entire list up to i
- insertAfter is \(O(1)\) if we get the memory address of the element to insert after.
- delete is:
SLL: {{c4::\(\Theta(l)\) as we need to find the previous element and change it's pointer}.}
DLL: \(O(1)\) we know the address of the previous element and then just edit it's pointer.
After
Front
- Insert is \(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\).
- Get is \(\Theta(i)\) very slow as we need to traverse the entire list up to i
- insertAfter is \(O(1)\) if we get the memory address of the element to insert after.
- delete is:
SLL: \(\Theta(l)\) as we need to find the previous element and change it's pointer.
DLL: \(O(1)\) we know the address of the previous element and then just edit it's pointer.
Back
- Insert is \(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\).
- Get is \(\Theta(i)\) very slow as we need to traverse the entire list up to i
- insertAfter is \(O(1)\) if we get the memory address of the element to insert after.
- delete is:
SLL: \(\Theta(l)\) as we need to find the previous element and change it's pointer.
DLL: \(O(1)\) we know the address of the previous element and then just edit it's pointer.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | In a <b>singly</b> and <b>doubly linked list</b>, the operation:<br><ul><li><b>Insert</b> is {{c1::\(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\). }}<br></li><li><b>Get</b> is {{c2::\(\Theta(i)\) very slow as we need to traverse the entire list up to <b>i</b>}}<br></li><li><b>insertAfter</b> is {{c3:: \(O(1)\) if we get the memory address of the element to insert after.}}<br></li><li><b>delete</b> is:<br> SLL: {{c4::\(\Theta(l)\) as we need to find the previous element and change it's pointer |
In a <b>singly</b> and <b>doubly linked list</b>, the operation:<br><ul><li><b>Insert</b> is {{c1::\(\Theta(1)\) as we know the memory address of the final element in the list and just have to set the null pointer to the new keys address. Without this pointer it's \(\Theta(l)\). }}<br></li><li><b>Get</b> is {{c2::\(\Theta(i)\) very slow as we need to traverse the entire list up to <b>i</b>}}<br></li><li><b>insertAfter</b> is {{c3:: \(O(1)\) if we get the memory address of the element to insert after.}}<br></li><li><b>delete</b> is:<br> SLL: {{c4::\(\Theta(l)\) as we need to find the previous element and change it's pointer.}}<br> DLL: {{c5:: \(O(1)\) we know the address of the previous element and then just edit it's pointer.}}</li></ul> |
Note 6: ETH::A&D
Note Type: Horvath Cloze
GUID:
Q3:!A9V`D,
Before
Front
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of Entry (Base Case, recursive formula, pay attention to bounds!)
- Calculation Order (what depends on what entries, what variable incremented first)
- Extract Solution (How to get final solution out)
- Running time proof
Back
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of Entry (Base Case, recursive formula, pay attention to bounds!)
- Calculation Order (what depends on what entries, what variable incremented first)
- Extract Solution (How to get final solution out)
- Running time proof

Smiling Monkey In Red Overall Steals Tacos
After
Front
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of entries (Base case, recursive formula, pay attention to bounds!)
- Order of calculation (what depends on what entries, what variable incremented first)
- Extracting the solution
- Runtime
Back
- Define the DP table (dimensions, index, range; meaning of entry): ex: DP[1..n+1][1..k+1]
- Computation of entries (Base case, recursive formula, pay attention to bounds!)
- Order of calculation (what depends on what entries, what variable incremented first)
- Extracting the solution
- Runtime

Smiling Monkey In Red Overall Steals Tacos
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | Steps of giving a DP solution:<br><ol><li>{{c1::Define the DP table (dimensions, index, range; meaning of entry): ex: <b>DP[1..n+1][1..k+1]</b>}}</li><li>{{c2::Computation of |
Steps of giving a DP solution:<br><ol><li>{{c1::Define the DP table (dimensions, index, range; meaning of entry): ex: <b>DP[1..n+1][1..k+1]</b>}}</li><li>{{c2::Computation of entries (Base case, recursive formula, pay attention to bounds!)}}</li><li>{{c3::Order of calculation (what depends on what entries, what variable incremented first)}}</li><li>{{c4::Extracting the solution}}</li><li>{{c5::Runtime}}</li></ol> |
| Extra | SMIROST (Size, Meaning, Initialisation, Recursive |
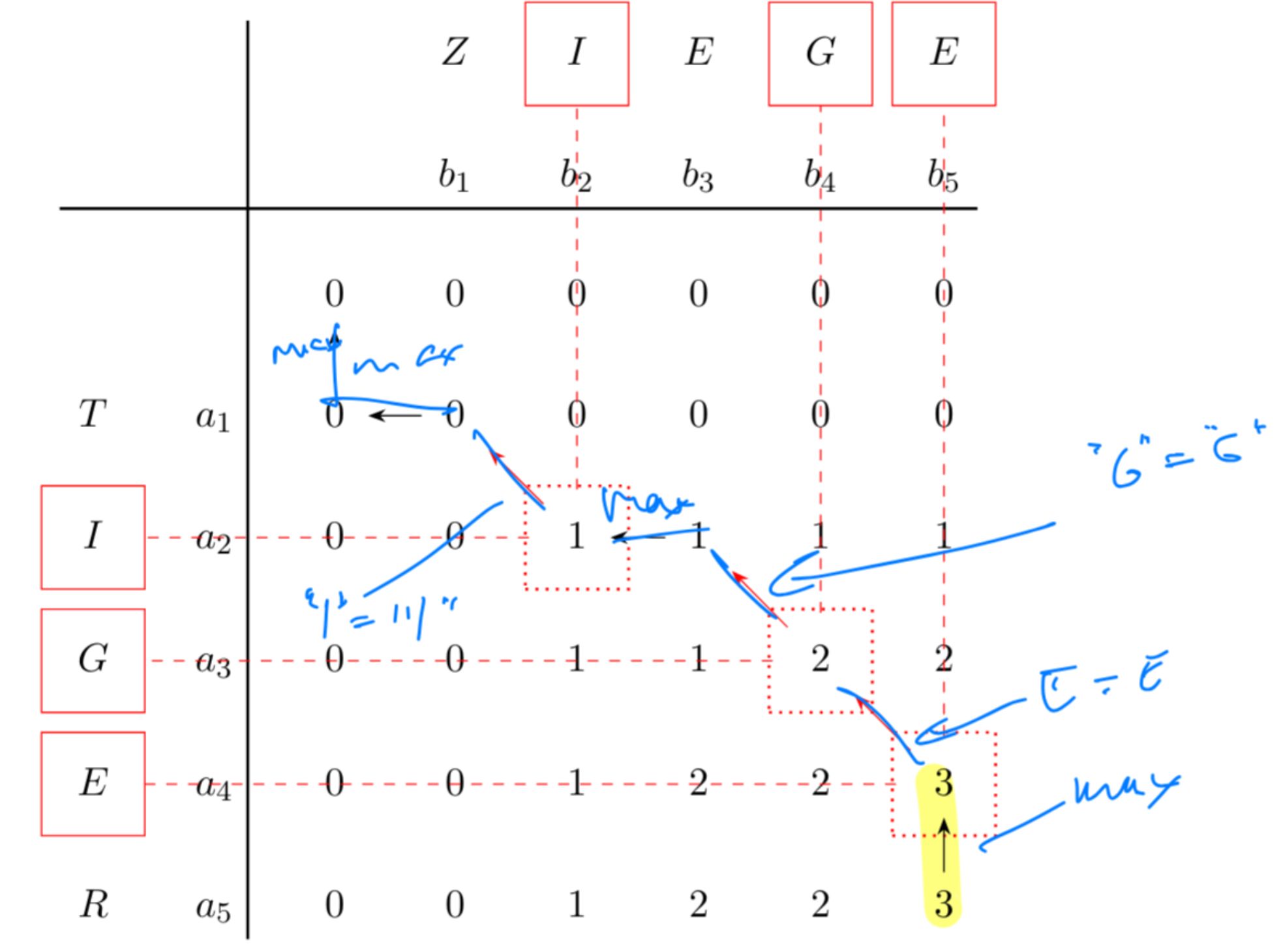
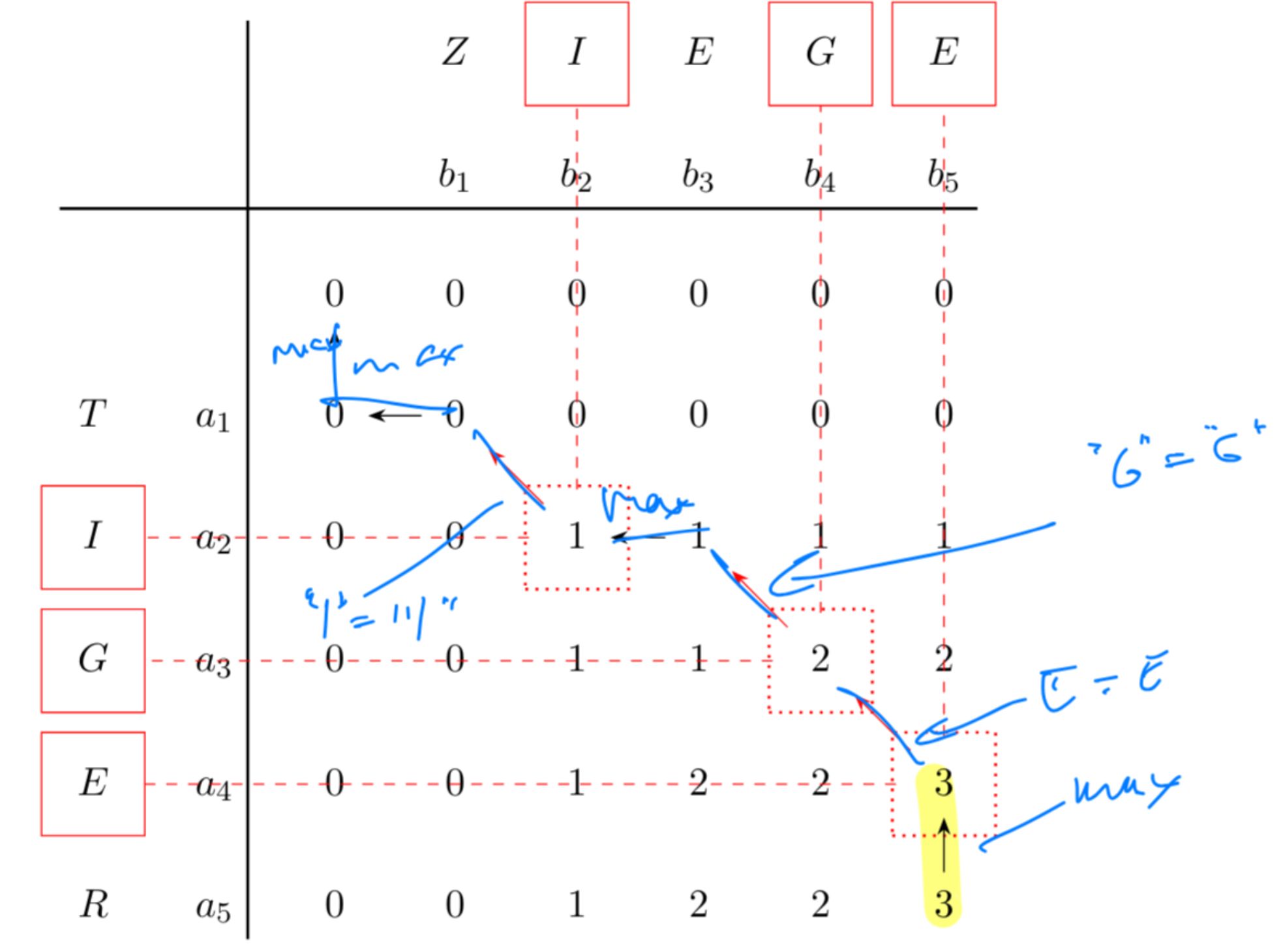
SMIROST (Size, Meaning, Initialisation, Recursive Relation, Order, Solution, Time)<br><br><img alt="" src="https://chatgpt.com/backend-api/estuary/content?id=file_00000000b144722fb24d37aefc63a244&ts=490704&p=fs&cid=1&sig=9139f521032b1f527f402bd9e46aa4fc98c1c346920ce78fa1198c460ce702b0&v=0"><img src="b8ad5128-8b94-4df8-a395-8fcd177c0ef6.png"><br><strong>S</strong>miling <strong>M</strong>onkey <strong>I</strong>n <strong>R</strong>ed <strong>O</strong>verall <strong>S</strong>teals <strong>T</strong>acos<img alt="" src="https://chatgpt.com/backend-api/estuary/content?id=file_00000000b144722fb24d37aefc63a244&ts=490704&p=fs&cid=1&sig=9139f521032b1f527f402bd9e46aa4fc98c1c346920ce78fa1198c460ce702b0&v=0"> |
Note 7: ETH::A&D
Note Type: Horvath Cloze
GUID:
QJ{Y%?s>+w
Before
Front
Back
After
Front
Back
Recursion: \(DP[i][B] = DP[i-1][B] \lor DP[i-1][B - b_i]\)
The term \(B - b_i\) can become negative. Instead of accessing an invalid index, return "false" (the neutral element for OR), since you can't achieve a negative sum.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | When writing |
When writing a recursion which accesses an index that could go out of bounds, make sure to {{c1::return a neutral value instead of crashing}}. |
| Extra | Example: Subset Sum<br><br>Recursion: \(DP[i][B] = DP[i-1][B] \lor DP[i-1][B - b_i]\)<br><br>The term \(B - b_i\) can become negative. Instead of accessing an invalid index, return "false" (the neutral element for OR), since you can't achieve a negative sum. |
Note 8: ETH::A&D
Note Type: Horvath Classic
GUID:
i~[|jYI|rt
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | What is "backtracking" in DP problems? | |
| Back | Once the DP table is filled, backtracking reconstructs the actual solution (not just the optimal value) by tracing which choices led to each cell.<br><br><img src="paste-c186a33203c3cb874cfeb7870ee1a4c5d52bf205.jpg"> |
Note 9: ETH::A&D
Note Type: Horvath Classic
GUID:
m5TC:^C`Y9
Before
Front
Back
set the inner loop variable to be the array's inner variable:
for j in ...:
for i in ...:
DP[j][i]
Otherwise we have to jump DP[i].length elements each time we want to access the next element
After
Front
Back
Set the inner loop variable to be the array's inner variable:
for j in ...:
for i in ...:
DP[j][i]
Otherwise we have to jump DP[i].length elements each time we want to access the next element.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | How to speed up array access for a DP-array | |
| Back | <b>Row-Major</b> vs. <b>Column Major</b> Access:<br><br> |
<b>Row-Major</b> vs. <b>Column Major</b> Access:<br><br>Set the inner loop variable to be the array's inner variable:<br><br>for j in ...:<br> for i in ...:<br> DP[j][i]<br><br>Otherwise we have to jump DP[i].length elements each time we want to access the next element. |
Note 10: ETH::A&D
Note Type: Horvath Classic
GUID:
vgCb-fRsjm
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | How can we get the runtime of an algorithm based on it's DP table? |
Note 11: ETH::DiskMat
Note Type: Horvath Classic
GUID:
Cug/az1F}r
Before
Front
Back
- Find \(B\) uncountable such that \(A \subseteq B\).
- Show that \(B \backslash A\) countable which proves that \(A\) uncountable.
- You have to prove this implication in the exam:
- Assume \(A\) is countable towards contradiction.
- We have shown that \(B \ \backslash \ A\) is countable.
- Thus \(A \cup (B \ \backslash \ A)\) also countable (Theorem 3.22: Union of countable is countable).
- But \(A \cup (B \ \backslash \ A) = B\) which is uncountable - contradiction!
Beispiel mit \([0,1] \setminus \mathbb{Q}\):
- We know \([0,1]\) is uncountable.
- By definition \([0, 1] \setminus \mathbb{Q} \subseteq [0,1]\) and \([0,1] \setminus ([0,1] \setminus \mathbb{Q})\) which is equal to \(\mathbb{Q} \cap [0,1]\). Thus \(\mathbb{Q} \cap [0,1] \subseteq \mathbb{Q}\) and by Lemma 3.15 \(\mathbb{Q} \cap [0,1] \preceq \mathbb{Q}\) (subset is dominated).
- Hence \(\mathbb{Q} \cap [0,1] \preceq \mathbb{N}\) (by transitivity).
- Therefore \(\mathbb{Q} \cap [0,1] = [0,1] \setminus ([0,1] \setminus \mathbb{Q})\) countable and thus \([0,1] \setminus \mathbb{Q}\) uncountable (by complement trick).
After
Front
Back
- Find \(B\) uncountable such that \(A \subseteq B\).
- Show that \(B \backslash A\) countable which proves that \(A\) uncountable.
- You have to prove this implication in the exam:
- Assume \(A\) is countable towards contradiction.
- We have shown that \(B \ \backslash \ A\) is countable.
- Thus \(A \cup (B \ \backslash \ A)\) also countable (Theorem 3.22: Union of countable is countable).
- But \(A \cup (B \ \backslash \ A) = B\) which is uncountable - contradiction!
Beispiel mit \([0,1] \setminus \mathbb{Q}\):
- We know \([0,1]\) is uncountable.
- By definition \([0, 1] \setminus \mathbb{Q} \subseteq [0,1]\) and \([0,1] \setminus ([0,1] \setminus \mathbb{Q})\) which is equal to \(\mathbb{Q} \cap [0,1]\). Thus \(\mathbb{Q} \cap [0,1] \subseteq \mathbb{Q}\) and by Lemma 3.15 \(\mathbb{Q} \cap [0,1] \preceq \mathbb{Q}\) (subset is dominated).
- Hence \(\mathbb{Q} \cap [0,1] \preceq \mathbb{N}\) (by transitivity).
- Therefore \(\mathbb{Q} \cap [0,1] = [0,1] \setminus ([0,1] \setminus \mathbb{Q})\) countable and thus \([0,1] \setminus \mathbb{Q}\) uncountable (by complement trick).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Uncountability Proof by Complement (with example \([0,1] \setminus \mathbb{Q}\): | Uncountability Proof by Complement (with example \([0,1] \setminus \mathbb{Q}\)): |
Note 12: ETH::DiskMat
Note Type: Horvath Classic
GUID:
G3,dI)){d{
Before
Front
Which elements generate \(\mathbb{Z}_n\)? Also proof
Back
Which elements generate \(\mathbb{Z}_n\)? Also proof
\(\mathbb{Z}_n\) is generated by all \(a \in \mathbb{Z}_n\) for which \(\gcd(n, a) = 1\) (all elements coprime to \(n\)).
Proof idea:
- If \(\mathbb{Z}_n = \langle a \rangle\), then \(1 \in \langle a \rangle\)
- This means \(au \equiv_n 1\) for some \(u\)
- By Bézout's identity, this implies \(\gcd(a, n) = 1\) (since \(\gcd\) must divide both \(au-qn\) and 1).
After
Front
Which elements generate \(\mathbb{Z}_n\)? How can this be proven?
Back
Which elements generate \(\mathbb{Z}_n\)? How can this be proven?
\(\mathbb{Z}_n\) is generated by all \(a \in \mathbb{Z}_n\) for which \(\gcd(n, a) = 1\) (all elements coprime to \(n\)).
Proof idea:
- If \(\mathbb{Z}_n = \langle a \rangle\), then \(1 \in \langle a \rangle\)
- This means \(au \equiv_n 1\) for some \(u\)
- By Bézout's identity, this implies \(\gcd(a, n) = 1\) (since \(\gcd\) must divide both \(au-qn\) and 1).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | <p>Which elements generate \(\mathbb{Z}_n\)? |
<p>Which elements generate \(\mathbb{Z}_n\)? How can this be proven?</p> |
Note 13: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
IH=>J8$0Y%
Before
Front
1. Set notation (subset of \(A \times B\))
2. Boolean matrix (1 if \((a,b) \in \rho\), 0 otherwise)
3. Directed graph (nodes are elements, edges are relations)
Back
1. Set notation (subset of \(A \times B\))
2. Boolean matrix (1 if \((a,b) \in \rho\), 0 otherwise)
3. Directed graph (nodes are elements, edges are relations)
After
Front
- Set notation (subset of \(A \times B\))
- Boolean matrix (1 if \((a,b) \in \rho\), 0 otherwise)
- Directed graph (nodes are elements, edges are relations)
Back
- Set notation (subset of \(A \times B\))
- Boolean matrix (1 if \((a,b) \in \rho\), 0 otherwise)
- Directed graph (nodes are elements, edges are relations)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | What are the three ways to represent a relation on finite sets?<br>< |
What are the three ways to represent a relation on finite sets?<br><ol><li>{{c1:: <strong>Set notation</strong> (subset of \(A \times B\))}}</li><li>{{c2:: <strong>Boolean matrix</strong> (1 if \((a,b) \in \rho\), 0 otherwise)}}</li><li>{{c3:: <strong>Directed graph</strong> (nodes are elements, edges are relations)}}</li></ol> |
Note 14: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
LM9=
Before
Front
- a large prime \(p\)
- basis \(g\) which is then exponentiated
Back
- a large prime \(p\)
- basis \(g\) which is then exponentiated
After
Front
- a large prime \(p\)
- a basis \(g\), which is then exponentiated
Back
- a large prime \(p\)
- a basis \(g\), which is then exponentiated
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | The Diffie-Hellman Key-Agreement selects two public values:<br><ol><li>{{c1:: a large prime \(p\)}}</li><li>{{c2:: basis \(g\) which is then exponentiated}}</li></ol> | The Diffie-Hellman Key-Agreement selects two public values:<br><ol><li>{{c1:: a large prime \(p\)}}</li><li>{{c2:: a basis \(g\), which is then exponentiated}}</li></ol> |
Note 15: ETH::DiskMat
Note Type: Horvath Classic
GUID:
M035/^ZEJ$
Before
Front
Back
if \(n\) is written \(n = p_1^{e_1} \times p_2^{e_2} \times ... \times p_k^{e_k}\) then it is \(\prod_{i=1}^k (e_i+1)\)
After
Front
Back
If \(n\) is written \(n = p_1^{e_1} \times p_2^{e_2} \times ... \times p_k^{e_k}\) then it is \(\prod_{i=1}^k (e_i+1)\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | The number of divisors of \(n\) (as the order of each subgroup divides the group order (which is n here) by Lagrange). <br><br>If \(n\) is written \(n = p_1^{e_1} \times p_2^{e_2} \times ... \times p_k^{e_k}\) then it is \(\prod_{i=1}^k (e_i+1)\) |
Note 16: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
N$(b/mcC}}
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Extra | Difference to group: |
Difference to group: Absence of inverse |
Note 17: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
eQKQ_hr,6l
Before
Front
We have the order {{c1::\(\text{ord}(a)\)}} = \(|\langle a \rangle|\). (Subgroup def.)
Back
We have the order {{c1::\(\text{ord}(a)\)}} = \(|\langle a \rangle|\). (Subgroup def.)
After
Front
We have {{c1::the order \(\text{ord}(a)\)}} = \(|\langle a \rangle|\).
Back
We have {{c1::the order \(\text{ord}(a)\)}} = \(|\langle a \rangle|\).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | <p>We have the order |
<p>We have {{c1::the order \(\text{ord}(a)\)}} = {{c2::\(|\langle a \rangle|\)::Subgroup definition}}. </p> |
Note 18: ETH::DiskMat
Note Type: Horvath Classic
GUID:
flg:zgN+=`
Before
Front
Back
- Assume countable: Suppose \(f: \mathbb{N} \to A\) is a bijection. Therefore we can enumerate elements of \(A\): \(a_1, a_2, a_3, \ldots\)
- Represent elements: Let \(a_{i,j} \) represent the \(j\)-th number in the \(i\)-th element.
- Construct diagonal element \(b\): Define \(b\) by setting each element
- We need to have: \(b_i \neq a_{i,i}\) for all \(i\)
- \(b_i = 1 - a_{i,i}\) (flip the bit) or \(b_i = \begin{cases} 4 & \text{if } a_{i,i} \neq 4 \\ 5 & \text{if } a_{i,i} = 4 \end{cases}\) (simply change element)
- Show \(b\) not in list: For any \(i\), we have \(b_i \neq a_{i,i}\)
- Therefore \(b \neq a_i\) for all \(i\)
- Contradiction: But \(b \in A\), yet \(b \notin \{a_1, a_2, \ldots\}\)
- So \(f\) is not surjective → no bijection exists → \(A\) uncountable
Key idea: \(b\) differs from the \(n\)-th element in the \(n\)-th position, so it "escapes" any enumeration.
After
Front
Back
- Assume countable: Suppose \(f: \mathbb{N} \to A\) is a bijection. Therefore we can enumerate elements of \(A\): \(a_1, a_2, a_3, \ldots\)
- Represent elements: Let \(a_{i,j} \) represent the \(j\)-th number in the \(i\)-th element.
- Construct diagonal element \(b\): Define \(b\) by setting each element
- We need to have: \(b_i \neq a_{i,i}\) for all \(i\)
- \(b_i = 1 - a_{i,i}\) (flip the bit) or \(b_i = \begin{cases} 4 & \text{if } a_{i,i} \neq 4 \\ 5 & \text{if } a_{i,i} = 4 \end{cases}\) (simply change element)
- Show \(b\) not in list: For any \(i\), we have \(b_i \neq a_{i,i}\)
- Therefore \(b \neq a_i\) for all \(i\)
- Contradiction: But \(b \in A\), yet \(b \notin \{a_1, a_2, \ldots\}\)
- So \(f\) is not surjective → no bijection exists → \(A\) uncountable
Key idea: \(b\) differs from the \(n\)-th element in the \(n\)-th position, so it "escapes" any enumeration.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | Uncountability Proof by Diagonalisation |
Uncountability Proof by Diagonalisation |
Note 19: ETH::DiskMat
Note Type: Horvath Classic
GUID:
lvTl-y(g+[
Before
Front
Back
- Injektion finden: Konstruiere \(f : {0, 1}^\infty \rightarrow A$, sodass $b \not = b’ \ \implies f(b) \not = f(b’)\)
- Funktion verifizieren: Zeige dass \(f\) well-defined und total ist, und \(f(b) \in A\) für alle \(b\).
- Injektivität beweisen: Zeige \(f(b) = f(b’) \ \implies b = b’\) oder direkt \(b \not = b’ \ \implies \ f(b) \not = f(b’)\).
- Schluss: We now know \(\{0, 1\}^\infty \preceq A\) as there's an injection.
Annahme \(A \preceq \mathbb{N} \implies \{0, 1\}^\infty \preceq \mathbb{N}\) via transitivity -> Contradiction. Thus \(A\) is uncountable: \(\lnot (A \preceq\mathbb{N})\).
After
Front
Back
- Injektion finden: Konstruiere \(f : {0, 1}^\infty \rightarrow A\), sodass \(b \not = b’ \ \implies f(b) \not = f(b’)\).
- Funktion verifizieren: Zeige dass \(f\) well-defined und total ist, und \(f(b) \in A\) für alle \(b\).
- Injektivität beweisen: Zeige \(f(b) = f(b’) \ \implies b = b’\) oder direkt \(b \not = b’ \ \implies \ f(b) \not = f(b’)\).
- Schluss: We now know \(\{0, 1\}^\infty \preceq A\) as there's an injection.
Annahme \(A \preceq \mathbb{N} \implies \{0, 1\}^\infty \preceq \mathbb{N}\) via transitivity -> Contradiction. Thus \(A\) is uncountable: \(\lnot (A \preceq\mathbb{N})\).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | <ul>
<li><em>Injektion finden</em>: Konstruiere \(f : {0, 1}^\infty \rightarrow A |
<ul> <li><em>Injektion finden</em>: Konstruiere \(f : {0, 1}^\infty \rightarrow A\), sodass \(b \not = b’ \ \implies f(b) \not = f(b’)\).</li> <li><em>Funktion verifizieren</em>: Zeige dass \(f\) <em>well-defined</em> und <em>total</em> ist, und \(f(b) \in A\) für alle \(b\).</li> <li><em>Injektivität beweisen</em>: Zeige \(f(b) = f(b’) \ \implies b = b’\) oder direkt \(b \not = b’ \ \implies \ f(b) \not = f(b’)\).</li> <li><em>Schluss</em>: We now know \(\{0, 1\}^\infty \preceq A\) as there's an injection.<br>Annahme \(A \preceq \mathbb{N} \implies \{0, 1\}^\infty \preceq \mathbb{N}\) via transitivity -> Contradiction. Thus \(A\) is uncountable: \(\lnot (A \preceq\mathbb{N})\).</li></ul> |
Note 20: ETH::DiskMat
Note Type: Horvath Classic
GUID:
pD<6]f{)8D
Before
Front
Back
After
Front
Back
( 1, 3, 7, 9, 11, 13, 17, 19 )
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | \(\varphi(\varphi(25)) = |\mathbb{Z}_{\varphi(25)}| = |\mathbb{Z}_{20}| = 8\) <br><br>( 1, 3, 7, 9, 11, 13, 17, 19 ) |
Note 21: ETH::DiskMat
Note Type: Horvath Classic
GUID:
qAyHDnFN7L
Before
Front
Back
2. if \(\mathbb{Z}_n^*\) is cyclic then it is isomorphic to \(\mathbb{Z}_{\varphi(n)}^+\) (by lemma)
3. the number of generators of \(\mathbb{Z}_{\varphi(n)}^+\) is \(\varphi(\varphi(n))\) as it is the number of coprime elements of the group
After
Front
Back
2. If \(\mathbb{Z}_n^*\) is cyclic then it is isomorphic to \(\mathbb{Z}_{\varphi(n)}^+\) (by lemma)
3. The number of generators of \(\mathbb{Z}_{\varphi(n)}^+\) is \(\varphi(\varphi(n))\) as it is the number of coprime elements of the group.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | 1. |
1. Verify that \(\mathbb{Z}_n^*\)is cyclic (iff n = 2, 4, \(p^e\), \(2p^e\), with \(e \ge 1\) and \(p\) is an odd prime)<br>2. If \(\mathbb{Z}_n^*\) is cyclic then it is isomorphic to \(\mathbb{Z}_{\varphi(n)}^+\) (by lemma) <br>3. The number of generators of \(\mathbb{Z}_{\varphi(n)}^+\) is \(\varphi(\varphi(n))\) as it is the number of coprime elements of the group. |
Note 22: ETH::DiskMat
Note Type: Horvath Classic
GUID:
tuHe#n^N^#
Before
Front
Back
That is, it's hard to find \(x_A\) from \(g^{x_A} \mod p\), knowing \(g\).
After
Front
Back
That is, it's hard to find \(x_A\) from \(g^{x_A} \mod p\), knowing \(g\).
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Front | The Diffie-Hellman Key-Agreement works because? |
Note 23: ETH::DiskMat
Note Type: Horvath Cloze
GUID:
uK|j,XZw5[
Before
Front
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Back
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
After
Front
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Back
They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is sent over the network to their partner.
The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}.
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | For D |
For Diffie-Hellman key agreement, both Alice and Bob {{c1:: choose \(x_A, x_B\) (their private keys) at random}}.<br><br>They then compute {{c2:: \(y_A := R_p(g^{x_A})\) and \(y_B\) analogously, which are their public keys}} which is {{c2:: sent over the network to their partner}}.<br><br>The other {{c3:: then exponentiates by their private key to get the shared key \(k_{AB} \equiv_p y_B^{x_A} \equiv_p g^{x_B \cdot x_A} \equiv_p y_A^{x_B}\)}}. |
Note 24: ETH::EProg
Note Type: Horvath Cloze
GUID:
D{XXurJu$`
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | {{c1:: short, int, float, double, long}} can be initialized using {{c2:: hexadecimal}} | {{c1:: short, int, float, double, long}} can be initialized using {{c2:: hexadecimal}}. |
Note 25: ETH::LinAlg
Note Type: Horvath Cloze
GUID:
Dd-0>Kd049
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | The columns of \(A\) are independent if and only if {{c1::\(x = 0\) is the |
The columns of \(A\) are independent if and only if {{c1::\(x = 0\) is the only vector for which \(Ax = 0\)::Linear combination view}}. |
Note 26: ETH::LinAlg
Note Type: Horvath Cloze
GUID:
D|B,=vwf}e
Before
Front
Back
After
Front
\(A(B+C)=AB + AC\)
Back
\(A(B+C)=AB + AC\)
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | For matrices |
For matrices \(A\), \(B\), \(C\):<br><br>\(A(B+C)={{c1::AB + AC}}\) |
| Extra | (Distributivity) |
Note 27: ETH::LinAlg
Note Type: Horvath Classic
GUID:
v`BTz<1Q{~
Before
Front
Back
After
Front
Back
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Back | Falls eine Matrix \( \mathbf{X} \) existiert, so |
Falls eine Matrix \( \mathbf{X} \) existiert, sodass \( \mathbf{AX} = \mathbf{XA} = \mathbf{I_n}\)<div><br></div><div>Beispiel: \( \begin{pmatrix} 1 & 2 \\ 0 & 3 \end{pmatrix} * \begin{pmatrix} 1 & -\frac{2}{3} \\ 0 & \frac{1}{3} \end{pmatrix} = \mathbf{I_2}\) </div> |
Note 28: ETH::LinAlg
Note Type: Horvath Cloze
GUID:
z~{N,b0:-A
Before
Front
Back
After
Front
Back
Lemma 2.11
Field-by-field Comparison
| Field | Before | After |
|---|---|---|
| Text | The {{c2::independent}} columns of \(A\) {{c1::span the column |
The {{c2::independent}} columns of \(A\), {{c1::span the column space \(\textbf{C}(A)\) of \(A\)}}. |
| Extra | Proven by induction, adding elements that are a linear combination of other ones doesn't change span, thus we can iteratively remove the dependent columns. | Proven by induction, adding elements that are a linear combination of other ones doesn't change span, thus we can iteratively remove the dependent columns.<br><br>Lemma 2.11 |